Following a nationwide search, the Office of the Provost has announced the appointment
of seasoned attorney and law school administrator, Ronald H. Weich, J.D., as the next
dean of Seton Hall School of Law. Read more >>
Seton Hall University School of Law will deliver its Denis F. McLaughlin Advanced
Trial Advocacy Workshop this coming January 2024. Read more >>
Seton Hall University Law School held its Fourth Annual Sports Law Symposium on Wednesday,
November 8, 2023, centered around the theme “Money in Sports,” and the evolving landscape
of investment in sports betting, sports media, and teams and leagues. Read more >>
Professor Gaia Bernstein recently had her Op-Ed "California is right: Addictive tech
design is not free speech" published in the Hill. Read more.
Seton Hall Law Professor Doron Dorfman received the Michael J. Zimmer Memorial Award
for a rising scholar who has made a significant contribution to the field of work
law. Read more.
In 2023, Seton Hall Law School named three members of our community to the Pro Bono
Honor Role to recognize the tremendous contributions they have made to both the University
and the community. Read more.
Mr. William Coppola joins Seton Hall Law as the Gibbon’s Institute for Law, Science
and Technology Distinguished Practitioner in Residence. Seton Hall Law enthusiastically
welcomes Bill and his extensive experience in patent, intellectual property, and transaction
matters to enrich the student experience and intellectual property legal learning
community. Read more.
Seton Hall Law Professor Jonathan Hafetz created and hosts the podcast Law on Film.
Law on Film explores the rich connections between law and film. Law is critical to
many films, even to those that are not obviously about the legal world. Read more.
Professor Sara Gras is hosting and producing Season 1 of the new podcast, “Hearsay
from the Sidelines” for Culture in Sports. Read more.
Editors compiled data in five categories: credibility, affordability, student outcomes,
student experience, and application process. The online MLS at Seton Hall was selected
in part because of the student experience: most students enroll part-time, taking
one course at a time and graduating within two years. Read more.
On September 7, 2023 Seton Hall Law’s Latin American Law Students Association (LALSA)
received the Hispanic National Bar Association’s (HNBA) “Vision in Action” Law Student
Organization of the Year Award. Accepting the award at the HNBA Annual Convention
were Co-Presidents, Taylor Lugo-Maestas ’24 and Justin Perez ’24, along with Natalia
Sifuentes ’24, LALSA’s HNBA representative. Read more.
Last week marked the start of the new academic year for the award-winning Leadership
Fellows Program, comprised of a selective cadre of Seton Hall Law students with demonstrated
leadership ability. Read more.
The Center for Policy & Research at Seton Hall University has released a report, "The
January 6 Insurrectionists: Who They Are and What They Did," which presents demographic
data and provides a detailed examination of the disposition and charges brought against
the 716 persons prosecuted in the first year after the storming of the Capitol. Read more.
Professor David Opderbeck has received a Fulbright U.S. Scholar Program award for
the 2023-2024 academic year from the U.S. Department of State and the Fulbright Foreign
Scholarship Board. Professor David Opderbeck will examine regional differences in
AI regulations and their impact on privacy and security. Read more.
At the annual awards ceremony for graduating students, held on May 24, 2023, the Center
for Social Justice (CSJ) recognized students for outstanding work and commitment in
each of its legal clinics. The CSJ also recognized one team of students overall for
their exemplary clinic work and one student overall for their excellence in the service
of our clients. Congratulations to the award recipients! Read more.
Seton Hall Law Professor Doron Dorfman and Professor Zackary Berger, M.D., of Johns
Hopkins School of Medicine, have published "Approving Workplace Accommodations for
Patients with Long Covid — Advice for Clinicians" in The New England Journal of Medicine.
Read more.
Professor Tracy Kaye guided law students from her EU Business Law course on a trip
through the EU Institutions of Brussels and Luxembourg over Spring break in early
March 2023. The trip was designed with the vision to provide an immersive learning
experience and cultural exchange with the EU to enrich the U.S. legal perspective
with an appreciation of the inner workings of European Institutions and their legal
system. Read more.
The Law School jumped 17 places to 56th overall and was ranked 12th best Part-Time
program and 11th best Health Care Law program in the nation. Read more.
Seton Hall Law Professor Gaia Bernstein's new book, Unwired: Gaining Control over
Addictive Technologies (Cambridge Press) has been generating buzz since its March
2023 release. Not only has the publication prompted news outlets, such as the Boston
Globe and Bloomberg, to interview Bernstein about her book, well-known magazines including
Wired, Time Magazine, and Fast Company have devoted significant space to the content
in the book. Read more.
Spearheaded by Lesley Risinger J.D.’03, the director of the Last Resort Exoneration
Project at Seton Hall Law, and Project co-founder, Professor Emeritus Michael Risinger,
the State of New York has vacated the conviction of Sheldon Thomas and released him
from custody. Arrested when he was 17, Thomas spent more than 18 years in prison under
a wrongful conviction for murder. Read more.
Each year, the Center for Social Justice selects second-year students to serve as
CSJ Scholars. Selected students include Fatima M. Abughannam ’24, Shaindy Black ‘25,
Eric Gallant ’24, Myron Minn-Thu-Aye ’25, and Jamie Mitrovic ‘24. Learn more about the program and selected students.
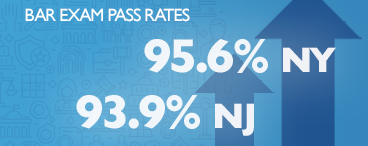
Seton Hall University School of Law ranked 31st in the nation for first-time bar passage
rate. According to statistics released by the American Bar Association for 2022 bar
exam takers, Seton Hall Law exceeded the New Jersey state average by more than 14
points with a pass rate of 85.71 percent compared to the state first-time pass rate
of 71.43 percent. Read more.
Fatima M. Abughannam ’24 is dedicated to advocating for criminal justice reform, particularly
as it relates to indigent defense and wrongful convictions. As a first-generation
American and daughter to Palestinian immigrants, Abughannam recognizes the importance
of enhancing access to justice and promoting fundamental rights for everyone, including
members of underrepresented groups. Read more >>
Shaindy Black ’25 is a first-generation weekend law student jointly pursuing her Master
of Social Work at the University of Pennsylvania. She plans to practice Family Law
using a trauma-responsive approach. Read more >>
Eric Gallant ’24 was led to Seton Hall Law by his commitment to helping others. In
2017, Eric entered Norwich University and earned a commission into the U.S. Army.
In his junior year, he pivoted in his career and decided to take the LSAT. He began
his legal path in 2021 at Seton Hall and will begin active-duty service as a JAG in
the Army upon graduation in 2024. Read more >>
Jamie Mitrovic ‘24 is committed to public interest by way of focusing on compliance
in environmental and energy law matters, while also serving BIPOC and other minority
communities around the tri-state area and beyond. More specifically, her primary plan
in the public service field revolves around the intersectionality of environmental
harms, disproportionate access to public services or environmental goods, and its
subsequent public health effects; all of which disproportionately affect BIPOC and
minority groups. Read more >>
Myron Minn-Thu-Aye ’25 grew up in Hong Kong. He majored in mathematics and computer
science at Williams College and completed his doctorate in mathematics at Louisiana
State University. He is a weekend student at Seton Hall Law and an Associate Professor
in Residence at the University of Connecticut, where he focuses on promoting accessibility
and active learning in mathematics. Read more >>
Seton Hall University School of Law’s groundbreaking program, the annual Gaming Law,
Compliance, and Integrity Bootcamp, is now underway. This year’s record attendance,
with over 100 participants, signals a growing demand in the gaming industry for in-depth
education about compliance, integrity, and ethics. Read more.
A group of nine Seton Hall Law students (and former students) received an award from
the New Jersey State Bar Association for their work in developing a series of informational
videos for survivors of domestic and sexual violence who represent themselves in restraining
order hearings. The students received the "Outstanding Law Student Pro Bono Award."
Read more.
For the first time the NJSBA is awarding a student pro bono award titled the “Outstanding
Law Student Pro Bono Awards” and the recipients will be two teams of Seton Hall Law
students - one of the teams being Professor Paula Franzese’s team of Leadership Fellows.
Read more.
Senior Practitioner in Residence Stephanie Norton of the Immigrants’ Rights/International
Human Rights Clinic at the Seton Hall Law School Center for Social Justice, along
with 3L student Michael Antzoulis, recently won a decisive precedential victory in
the United States Court of Appeals for the Third Circuit on behalf of their indigenous
Guatemalan client, Selvin Saban-Cach. Read more.
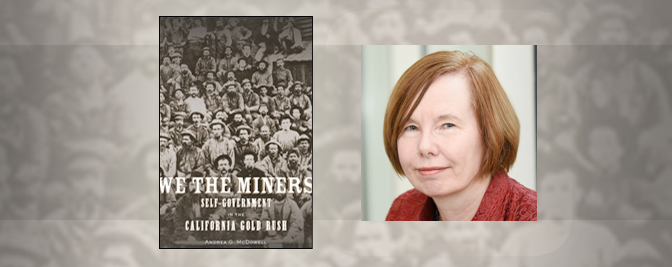
Professor Andrea McDowell’s book We the Miners: Self-Government in the California
Gold Rush was just named one of the ten best history books of 2022 by The Financial
Times. Read more.
Dean Kathleen M. Boozang announces her return to the Seton Hall Law faculty and Professor
John Kip Cornwell is named Interim Dean. The entire Seton Hall community thanks Dean
Boozang for her tireless devotion to Seton Hall Law, and for her continued service
to the University — her academic home since 1990. Read more.
Professors John V. Jacobi and Tara Adams Ragone continue to work with public and private
partners to build sustainability for workforce members who help address care and service
gaps for vulnerable populations. Read more.
Professors John V. Jacobi and Tara Adams Ragone will spearhead work on two projects
earmarked in the State of New Jersey’s 2022-23 budget. Read more.
The Center for Health & Pharmaceutical Law’s dynamic and highly-regarded faculty research,
write and present on the leading health law issues including technology addiction,
leadership during crisis, medical misinformation, cost-effective analysis in medication
coverage, impact of COVID on undocumented individuals, the legal treatment of the
use of Pre-exposure prophylaxis, disability law, third-party accommodations, conflicts
of interested in doctor-patient relationships, illegal activities and criminality
of pharmaceutical and medical device companies, violation of federal Medicare and
Medicaid rules with overlapping surgeries, DOJ’s FCA resolutions and enforcements,
community health workers, and improving healthcare access to vulnerable populations
to list a few. Read about their recent accomplishments.
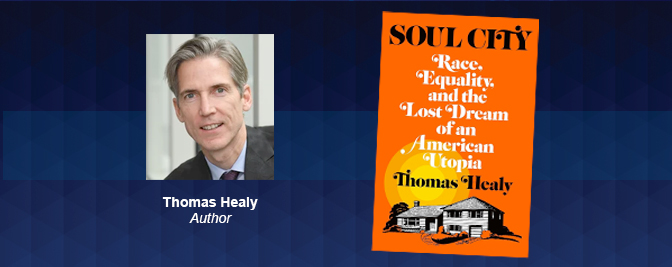
Professor Thomas Healy has received the 2021 Hooks National Book Award for his most
recent book, Soul City. The Hooks Institute’s National Book Award is presented to
a non-fiction book published in the calendar year that best furthers understanding
of the American civil rights movement and its legacy. Read more.
The Office of Career Services is excited to announce the opening of its second-hand
career closet for students. One of the challenges some students face when entering
law school and pursuing career opportunities is accessing appropriate professional
attire for career fairs, interviews, networking events, and other career related needs.
The CS Boutique aims to provide students with attire that will boost their confidence
and exude professionalism. Read more.
Joel Silver is a Senior Associate General Counsel at Gilead Sciences, Inc. in Foster
City, CA where he is responsible for managing global legal support for regulatory.
Joel also serves as the Chair of Gilead’s Pro Bono program, which is focused on helping
survivors of domestic violence obtain protective orders as well as providing vital
legal services for juvenile immigration cases.
Governor Phil Murphy announced his nomination of New Jersey Appellate Division Judge,
Douglas Fasciale, to become a justice on the New Jersey Supreme Court. He would be
the 42nd justice in the Court’s 75-year history. Judge Fasciale graduated Seton Hall
University with a bachelor’s in History in 1982, and he earned his J.D. from Seton
Hall Law School in 1986. Upon finishing school, he clerked for Superior Court Judge
John E. Keefe and thereafter worked as a trial lawyer in private practice for nearly
two decades. Read more.
Seton Hall University School of Law announces a new format for its Data Privacy and
Security Compliance Certificate Program with flexible Virtual Bootcamp Modules. Learners
will have the ability to bundle all bootcamp modules at a discounted rate or customize
and choose one or more modules to level-up privacy and security knowledge and skills.
Read more.
Associate Dean Solangel Maldonado co-founded and organized the Graciela Olivárez Latinas
in the Legal Academy Workshop (“GO LILA”) which launched this summer with a spectacular
inaugural meeting. Legal and cultural luminaries, including Supreme Court Justice
Sonia Sotomayor and Poet Laureate of Philadelphia Raquel Salas Rivera, spoke at the
event. By the time the 2-day conference concluded, over 70 current and aspiring Latina
law professors participated. Read more.
Just days before the student loan repayment pause was set to expire, President Biden
announced an extension of the payment pause and interest accrual until December 31,
2022. President Biden also announced that he is canceling $10,000 in student debt
for millions of borrowers. Read more.
Seton Hall Law School extends its sincere gratitude to The Honorable Esther Salas,
United States District Judge for the District of New Jersey for addressing incoming
1L students at Orientation during a conversation with the Dean. Judge Salas spoke
candidly about her journey to and through law school, her experience as a federal
public defender and how she realized she wanted to become a federal judge. Read more.
Assistant Professor Robert Boland joins Seton Hall Law as part of our Gaming, Hospitality,
Entertainment and Sports Law (“GHamES”) initiative and will focus on developing and
expanding Seton Hall’s Sports Law offerings. He brings a wealth of experience to this
endeavor, having most recently served as the Athletics Integrity Officer at the Pennsylvania
State University, where he oversaw the athletic program’s compliance with all legal
and ethical standards required by law, the University, the Big Ten and the NCAA. Learn more.
Seton Hall Law has earned the honor of producing the most graduates on the ROI Influencers: Law list. When interviewed by ROI, Dean Kathleen Boozang credits the strong alumni network
for part of the school’s success. Read more.
“Recent polling revealed that [The Court's] public approval is at an all-time low,
and that was before its latest week of controversial rulings. Notably, the most pronounced
turn in favorability coincided with the recent shift to a 6-3 split in favor of Republican-appointed
justices.” Read more.
We are pleased to welcome former L.E.O. student The Honorable Zoila Cassanova back
to Seton Hall Law School as the Director of the Legal Education Opportunity Program.
In this role, Judge Cassanova will be overseeing the administration of the Summer
LEO Institute and all LEO programming and events during the school year. Read more.
Seton Hall Law Alumnus and Adjunct Professor, K. Anthony Thomas, ‘95, has been named
the Acting Federal Public Defender for the District of New Jersey. While occupying
this vital and prestigious position, Mr. Thomas will oversee the office’s representation
of indigent defendants in the federal district court. Read more.
On May 25th, the United States Senate confirmed Seton Hall Law alumna, Evelyn Padin,
’92, to serve as a federal judge on the U.S. District Court for the District of New
Jersey. Ms. Padin, who founded her own law practice, was recently the president of
the New Jersey State Bar Association. She was the first Latina to serve in the role.
She is currently the co-chair of the Diverse Attorneys of Seton Hall (DASH) Advisory
Committee.
After graduation, CSJ Scholar Matthew Handley ’22, will start a fellowship at the
National Veterans Legal Services Program in Washington, D.C., sponsored by Lockheed
Martin Corp., as part of the Equal Justice Works Design Your Own Fellowship program.
Each year, the Center for Social Justice selects students from those who have completed
their first year of law school to serve as CSJ Scholars. Selected students include
Sam Jerabek ’23 and Florencia Marino ’24. Learn more about the program and selected students.
Seton Hall Law School’s Third Annual Gaming Law, Compliance & Integrity Bootcamp successfully
brought together regulators, operators, vendors, academics, law enforcement personnel,
and attorneys to discuss challenges facing the gaming industry and how to identify
and adopt best practices to promote compliant, ethical, responsible, and sustainable
gaming. Read more.
Philip R. Sellinger will join the faculty of Seton Hall University School of Law’s
Third Annual Gaming Law, Compliance, and Integrity Bootcamp on May 18, 2022, in Newark,
New Jersey. Read more.
Gibbons Institute for Law, Science & Technology and the Institute for Privacy Protection
presents a suite of virtual programs to equip compliance and legal professionals with
the knowledge they need to distinguish themselves as leaders in data privacy and security.
Learn more.
The latest research paper by Michael Fasciale, a 3L who is both Articles Editor of
the Seton Hall Law Review and President of the school’s Entertainment and Sports Law Society, has won multiple
honors. Fasciale wrote The Patchwork Problem: A Need for National Uniformity to Ensure an Equitable Playing
Field for Student-Athletes’ Name, Image, and Likeness Compensation, as a Comment for the Law Review. Read more.
The Law School is delighted that Professor Doron Dorfman is joining its ranks this
summer. While Professor Dorfman is known as an expert in Health and Disability Law,
he is an innovative scholar whose research defies simple categorization. Read more.
The judge used this year’s Diversity Speaks event to analyze the public response to
the nomination of the Honorable Ketanji Brown Jackson and carefully explained the
flawed assumptions of commentators’ critiques calling into question her qualifications
for the position after President Biden promised during his campaign to nominate a
black woman to the Court. Read more.
Seton Hall Law School’s Assistant Dean Devon Corneal outlined potential legal issues
facing the esports betting sector for ROJ-NJ's March 9, 2022 article on the rise of
esports in New Jersey. Read more.
The Impact Litigation Clinic in the Center for Social Justice recently prevailed in
a noteworthy, precedential Second Circuit decision, Triolo v. Nassau County, involving
false arrest, qualified immunity, and municipal liability. The Impact Clinic provides
pro bono representation to litigants and serves as amicus curiae in cases presenting
important legal issues on behalf of impoverished and disempowered litigants, generally
in the federal courts of appeals or in the Supreme Court of New Jersey. Read more.
Professor Isis Misdary will join Seton Hall Law in July to helm our Criminal Justice
Clinic. In this role, Professor Misdary will supervise clinical students on direct
criminal defense representation and broader strategic litigation. She will also lead
our efforts to design and pursue law reform projects in areas of dire need, such as
reentry, prisoner’s rights, expungement, or other aspects of criminal justice reform.
Read more.
On March 5, 2022, Seton Hall’s Interscholastic Moot Court Board won TWO National Moot
Court Competitions, finishing First in both the Bryant Moore National Civil Rights Moot Court Competition and the Gabrielli National Family Law Moot Court Competition. Read more.
On March 4, 2022, Seton Hall Law School Assistant Dean Devon Corneal sat down with
the New Jersey Law Journal to discuss the expansion of sports betting in New Jersey
and the need for comprehensive and robust compliance education for gaming operators.
Read more.
This evening’s conversation arises from a patient care conflict that has received
national attention over the last weeks as it turned into a national conversation about
the allocation of limited resources during the COVID pandemic. In this interdisciplinary
conversation, experts in law, medicine, and ethics will explore how hospitals are
coping and how lawmakers are responding. Read more.
With funding from the Legislature, Seton Hall Law School and Rutgers Law School established
the New Jersey Housing Justice Project at the start of the 2021-22 academic year.
The Housing Justice Project is expanding individual representation as it advocates
for broader social change, including work in the area of the implementation of landlord-tenant
reform and equity impact analysis in the landlord-tenant arena. Read more.
The Gibbons Institute for Law, Science & Technology and the Institute for Privacy
Protection is co-hosting this virtual conference to explore issues from U.S. and international
perspectives with leading academics, practitioners, and former regulators. Read more.
Seton Hall University's Chair of the Board of Regents, Kevin H. Marino, Esq. '84,
announced last month that he and his wife, Rita Marino, M.A.E. '94, are donating $1
million to establish an endowed professorship at Seton Hall University School of Law.
The professor occupying the endowed chair will be known as the Marino Tortorella &
Boyle Professor of Law, named for Marino's law firm. His partners, John D. Tortorella,
Esq. '99, and John A. Boyle, Esq. '00, are both distinguished Seton Hall Law alumni.
Read more.
To commemorate Black History Month, Uplands TV of the UK will air the documentary
One Thousand Years of Slavery – The Untold Story on the Smithsonian Channel. Four-Part
Docu-Series begins February 7, 2022.
When Daniel R. Levy ’04 learned the outsized impact on the Law School of increasing
its endowment, he swung into action. Dan was particularly engaged by the idea that
endowed scholarship funds could boost the Law School’s rankings by helping to recruit
and retain amazing students. He immediately turned to fellow Alumni Council members
Marc A. Calello ’89, Julian Leone ’04, and John Chiaia ’93 and the Chiaia Family who
are proud to announce the establishment of the Alumni Council Endowed Scholarship
fund. Read more.
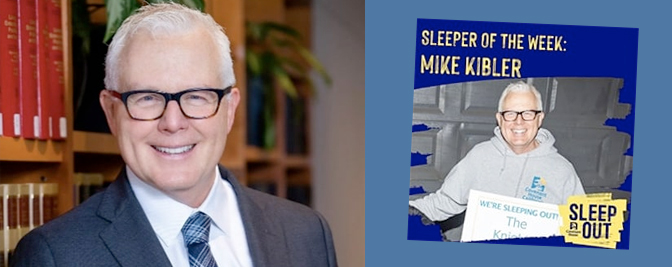
Double Pirate, Michael Kibler B.A.’92, J.D.’97, is no stranger to servant leadership.
The core principles he learned as a student helped to prepare him to be the leader
he is today. In addition to being a long-standing supporter of Seton Hall Law, Mike
volunteers for worthy organizations such as Covenant House California. This fall marked
his 9th year serving on the Board and participating in the Executive Sleep Out for
CHC. Read more.
The Christie Institute for Public Policy and Seton Hall University School of Law will
host a conversation with former United States Secretaries of Defense Leon Panetta
(2011-2013) and General James Mattis (2017-2018) at the Series on Public Service on
Thursday, December 16, 2021, from 7:00-8:00 p.m. on the importance and benefits of
bi-partisan public service to our nation. Learn more.
The Immigrants’ Rights/International Human Rights Clinic of the Center for Social
Justice has been participating in New Jersey’s Detention and Deportation Defense Initiative
(DDDI) since its launch in 2018. The State-funded Initiative enables Legal Services
of New Jersey, American Friends Service Committee, Rutgers Newark Law School’s Immigrant
Rights Clinic, and Seton Hall Law School’s Immigrants’ Rights/International Human
Rights Clinic to provide free legal representation to indigent New Jersey immigrants
facing deportation. Read more.
The Center for Health & Pharmaceutical Law is proud of its alumni accomplishments.
Our alumni continue to rise to prominence in their careers while uplifting their respective
industries and fields. Read full list of our alumni accomplishments.
The Center for Health & Pharmaceutical Law will host its Annual Health Law Symposium,
Long Term Care Services and Supports (LTSS): Payment and Caregiving on March 1, 2022.
Read more .
Professors John Jacobi and Tara Ragone are heading the Center for Health & Pharmaceutical
Law’s work as key partners in the execution of a new grant from the CDC: Community
Health Workers (CHW) for COVID Response and Resilient Communities. Through this three-year
grant, they will work with state agency and private sector partners to deploy CHWs
in prisoner reentry, behavioral health, and FQHC settings. Read more .
The team defeated UNH, UNM, South Texas, Hastings, and Loyola Chicago before losing
by a slight margin to Texas Tech in the Finals. This is the third year in a row that
Seton Hall has been in the Final Round at the competition - with two victories the
last two years. Read more .
This Thanksgiving, our deepest gratitude is owed to the scientists and medical professionals
who worked nonstop to develop vaccines and treatments, and to public health experts
and government leaders who assure their wide and fair distribution. Read more.
Seton Hall Law celebrates Judge Michael Chagares’ elevation to become Chief of the
Third Circuit, effective December 4, 2021. This is an extraordinary accomplishment
that shows the power of a Seton Hall Law degree. Read more.
After nearly a two-year pause, federal student loan payments are scheduled to resume
early in 2022. Additionally, your servicer may have changed since you graduated.
We are happy to help you navigate various repayment options. Learn more about recent changes.
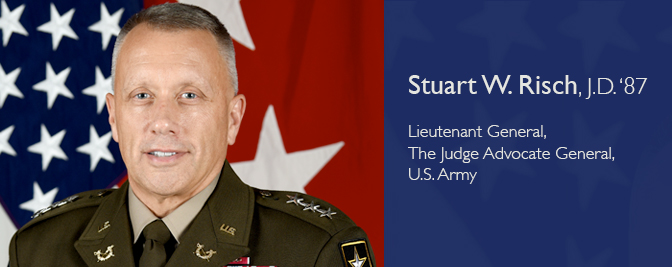
Seton Hall Law School proudly hosted Lieutenant General Stuart W. Risch, J.D. ’87,
The Judge Advocate General of the United States Army on November 10, 2021, as part
of Veteran’s Appreciation Week. LTG Risch spoke about the meaning of Veterans Day,
and he explained how law students can get involved in the JAG Corps and why they should
consider careers in service. LTG Risch also provided a stellar example of the meaning
of Veterans Day through his heartfelt words and demeanor, both of which encompassed
a common theme – gratitude. Read more.
Named from the red vestments used in celebrating the Mass and from the red robes worn
by judges in the Middle Ages, the Red Mass is celebrated at the beginning of the judicial
year to invoke God’s blessing and guidance in the administration of justice. The 2021
honoree recipient of the St. Thomas More Medal, The Honorable Joseph A. (Drew) Dickson
U.S.M.J. (retired) ’81 was joined by gift presenters Susan A. Feeney, Jeralyn Lawrence
’96, and Eileen M. O’Connor ’88 (not pictured), and readers Patrick D. Tobia ’85 and
the 2020 Red Mass honoree, K. Anthony Thomas ’95. View photos.
The Institute for Privacy Protection and the Gibbons Institute of Law, Science & Technology presents the Law and the Technologies of Life Colloquium. The Fall 2021 Colloquium is hosted by Professor Gaia Bernstein and will feature academic
speakers presenting cutting-edge projects on how new technologies change the way we
live and the role of the law in accommodating these technological innovations. Read more.
Professors Charles Sullivan and Mark Denbeaux were instrumental in making Seton Hall
Law the institution it is today. Together with others of their generation, they were
instrumental in creating and executing the vision that produced One Newark Center.
With all the gratitude for their years of service, teaching, practice, and pioneering,
we thank Professors Sullivan and Denbeaux and wish them utmost happiness and fulfillment
in the next chapter of their lives. Read more.
Assistant Dean of Career Services June K. Forrest has transformed Seton Hall Law’s
presence in New Jersey since her arrival in 2016, working with students and graduates
to discover their pathway to launching their careers, whether in the law or another
professional universe. Under Dean Forrest’s leadership, the Office of Career Services
(OCS) has become a place that welcomes all students. In partnership with our ever-loyal
alumni, the OCS team has captured employers across the New Jersey and New York marketplaces
and expanded Seton Hall Law’s reach to the many states from which admissions has increased
its recruitment. Read more.
ROI-NJ issued its annual “Influencers List,” for Higher Education, and Dean Kathleen
Boozang was given the honor of being declared an influencer among Deans and Directors
of Higher Educational Institutions. Read more.
Christopher Dernbach’21 and Mikayla Berliner ’21, students in the Impact Litigation
Clinic in the Center for Social Justice (CSJ),drafted an amicus brief in the Supreme
Court of New Jersey that played a significant role in the Court’s decision in State
v. McQueen. Professor Jon Romberg supervised the students and argued before the Court.
Read more >>
Willingness to work determinedly for those in need. Perseverance in the face of challenge.
These are the characteristics that define a Seton Hall Law School Center for Social
Justice (CSJ) Scholar. In the Fall semester of each year, the CSJ selects students
from those who have completed their first year of law school to serve as CSJ Scholars.
Selected students include Mia Dohrmann '22, Hannah Eaves '22, Matthew Handley '22
and Prubjot Kaur '22. Learn more about the program and selected students.
Mia Dohrmann ’22 was led to Seton Hall Law by the drive to serve communities and further
the cause of social justice. In 2012, she entered college in Baltimore with a goal
to become a doctor serving patients in disadvantaged communities. When she deviated
from the pre-medical path, she knew that she needed to utilize her passion for serving
others in a different way. After her graduation in 2016, she embarked on a 70-day
team bike ride from Baltimore to Seattle with the 4K for Cancer. During her journey,
her team met countless individuals affected by cancer who were still determined to
find a cure and help others facing tough diagnoses. Read more >>
Hannah Eaves ’22 came to Seton Hall Law to learn how to become an advocate for marginalized
members of our society. Eaves has focused her advocacy on the intersectionality between
socioeconomic status, health, race, and the law. “The social determinants of health
affect individuals’ access to economic resources, their statistical likelihood of
incarceration, and even their access to the franchise. We must understand all these
variables to develop the effective tools for changes,” said Eaves. She is concentrating
in Health Law, with the hopes of pursuing a career dedicated to ensuring health equity
for those with who have historically been underserved by the system and advocating
for anti-racist health policy. Read more >>
Prubjot Kaur ’22 is a first-generation law student who aspires to defend those disenfranchised
by the current legal system. “Minorities in the United States constantly undergo daily
interactions which exhibit the profound racism prevalent in our society. Racist experiences
have empowered me to vocally oppose bigotry of all forms and be committed to dismantling
systems of oppression to promote access to justice,” said Kaur. Read more >>
Ariel Risinger, JD ’15, an associate attorney at Day Pitney, recently made headlines
in Law360 Pulse for her accomplishments in competitive powerlifting. When asked about
her approach to competitions she told Law360 Pulse "I'm just going to go out there
and do my best, regardless if it's as a lawyer, or in powerlifting, or in whatever
I do." Read more >>
Professor Stephen Lubben testified regarding a bill that will require professionals
retained in Puerto Rico’s bankruptcy to disclose their stakes in connection with the
case. Read more >>
Professor Thomas Healy featured in a New York Times story on a noteworthy First Amendment
case. Read more >>
Luke Dodge ’21, Fran Mangot ’21, and Avi Muller ’21, under the auspices of the Impact
Litigation Clinic in the Center for Social justice, filed an amicus brief that significantly
informed the New Jersey Supreme Court’s decision in the very important case of State
v. Andujar; Professor Jon Romberg argued before the Court. Read more >>
On July 16, 2021, in a ceremony surrounded by family and friends, Seton Hall Law School
Alum Stuart W. Risch, J.D. ’87 was promoted to Lieutenant General (LTG) and sworn
in as The 41st Judge Advocate General of the United States Army. LTG Risch now leads
a Regiment 10,000 strong, comprised of judge advocates, enlisted paralegals, warrant
officers, as well as civilian attorneys and paraprofessionals. Read full story >>
Seton Hall Law congratulates Domenick Carmagnola ’88, Member at Carmagnola & Ritardi,
LLC, on being sworn in as the 123rd President of the New Jersey State Bar Association
for 2021-2022. Domenick values hard work and dedication and is not shy about strong
advocacy for the legal profession as we emerge from the pandemic. Hear more from Domenick’s installation speech on May 26.
Seton Hall University will be celebrating the official commemoration of Juneteenth
as a holiday in New Jersey. In September 2020, Governor Murphy signed legislation
formally designating Juneteenth as a recognized state and public holiday, which will
occur annually on the third Friday in June. Read more >>
Weekenders volunteered time at the local soup kitchen and gave back to the Newark
community; they worked on behalf of real clients through the Seton Hall Law’s Center
for Social Justice and wrote for Incarcerated Persons Workforce Re-Entry; and they
visited detainees at the border to provide legal services. Many students were instrumental
in starting and reviving new committees and student organizations throughout the law
school, with some assuming prominent leadership positions on the Law Review and in
the Student Bar Association, and achieving high placements in in Mock Trial and Moot
Court competitions. Read more.
Congratulations Seton Hall University School of Law Class of 2021! We’ve come a long
way since 1L. Each and every one of us should be so proud of all that we’ve accomplished
during our time at Seton Hall. Professor Murray gave a stirring speech at the 2020
orientation on what it means to become and practice as a lawyer during these times.
Read more >>
"You can’t let people rent space in your head. Don’t focus on how seemingly far ahead
or behind you are. The more time you spend worrying about someone else, the less time
you spend concentrating on your race. And, if you trust in these words, when you cross
that finish line, I promise you’ll be happy." Read full address >>
"Remember the classmates who helped you get there and remember that you did not do
this alone. We are all very fortunate to be receiving a degree from a University where
the sky really is the limit...if there is one thing you take away from this speech,
let it be this. Work hard, but don’t work so hard that you miss out on all of the
amazing things life has to offer. Because at the end of the day the things that give
our lives meaning are the people we surround ourselves with and the memories we make
along the way. The hero inside all of us should never fear living each moment to its
fullest." Read full address >>
"For someone on the right path, work is a central component of a life that includes
ample time for family and friends, for volunteerism and community service, and for
whatever else appeals to the mind and soul, be it music or art, prayer or literature,
film or sports, all of the above or countless other pursuits. Well‐rounded, happy
lawyers can and must have such things in their lives. You really can write the brief,
argue the appeal, negotiate the contract, lobby the legislature and still coach your
son or daughter’s basketball team. I promise." Read more.
"It is my hope that none of you ever forget the spot you have earned in this profession.
May none of us forget where we have come from and the lessons we learned together
in law school. If we remember this journey as we move up in our careers, I have no
doubt that we will continue to make an impact for the better in every courtroom, law
firm, or board room that we find ourselves in." Read full address >>
"Seton Hall lawyers are exceptional, and genuinely good and decent human beings.
And by graduating today, you are part of that enduring legacy of excellence and goodness.
Be proud of it and cherish it, like I do. You are a Seton Hall lawyer. It means
something. And because of that, each one of you is especially prepared to change
your corner of the world for the better." Read full keynote address.
In one program, Thomas Healy explores the failed social experiment of a community
based on principles of black economic empowerment, Soul City. In another, he examines
the mystery of one judge’s change in position about free speech, how that moment changed
the minds of others, and whether it’s time to change minds again. Read more >>
The Asian Pacific American Law Students Association (APALSA) at Seton Hall Law have
been busy hosting events and programs in celebration of the Asian American Pacific
Islander Heritage Month. Read more >>
Professor Marina Lao, who specializes in Antitrust Law, was interviewed by Christine
Hatfield on April 15 (WGLT 89.1 FM, NPR from Illinois State University) and provides
insight on what is best for consumers in latest nationwide debate over the options
consumers have to buy cars. Read more .
Law Professor Heather Payne is an emerging leader in the areas of environmental law,
energy law, evolving regulatory policy, and the implications for property, both real
and intellectual. Read more >>
Professor Alvin Richardo (Rick) Little has been appointed to be a Superior Court Judge
in Essex County. Throughout his distinguished career, Judge Little has carried himself
with grace and demonstrated a strong work ethic and commitment to justice, fairness,
and equity. Join us in congratulating Judge Little. Read more >>
Professor Emeritus Bernard K. Freamon has launched a website, entitled Ijmāʿ-on-Slavery.
The ambitious enterprise provides the first online platform for Muslim thinkers to
reach an agreement or “ijmāʿ” that slavery must be abolished under the Shari’a—the
authoritative corpus of texts on Islamic law and ethics. Dr. Freamon argues that the
Islamic legal concept of ijmāʿ (“consensus”) has the capacity to bring about powerful
social change. Read more >>
Seton Hall University School of Law’s Center for Social Justice (CSJ) prevailed in
Haley v. Board of Review, a case challenging the denial of unemployment benefits to
Newark resident Clarence Haley based upon his pretrial incarceration for charges later
dismissed. The New Jersey Supreme Court reversed the Appellate Division’s decision
denying Haley benefits and held that under New Jersey’s Unemployment Compensation
Law “pretrial detention is not an absolute bar” to benefits. Read more >>
As the 100th anniversary of the Chinese Communist Party approaches this July, officials
and media outlets from around the globe are contacting Law Professor Margaret "Maggie"
Lewis to provide her expertise and analysis of the legal policy implications today
concerning China and Taiwan with an emphasis on criminal justice and human rights.
Read more >>
Seton Hall Law ranked 47th in the country in the National Law Journal/LAW.COM list of Go-To Law Schools. The
survey ranks schools according to the percentage of graduates who get jobs at the
largest 100 law firms in the country. Read more >>
Celebrating Women in the Law: Seton Hall Law is incredibly proud to highlight some
of the recent achievements of its accomplished faculty in celebration of International
Women’s Day.
Read more >>
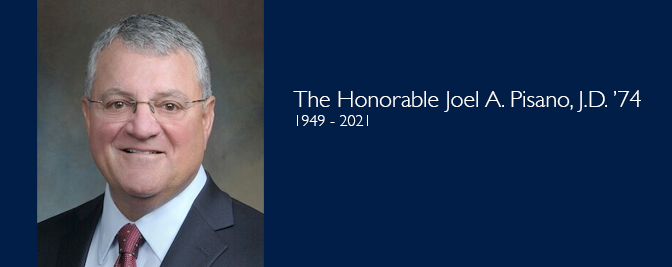
Seton Hall University School of Law mourns the passing of the Honorable Joel A. Pisano,
J.D. ’74, who was an adjunct professor and served as a federal judge in The United
States District Court for the District of New Jersey over the span of two decades.
Read more >>
Seton Hall University School of Law is saddened by the death of Professor Emeritus
Livingston Baker who passed away recently. He specialized in teaching property law
and public and private international law courses. Having taught over thirty years
at Seton Hall Law, including guest lectures at the School of Diplomacy, his teaching
repertoire was vast. Most importantly, Professor Baker’s discussions, both in class
and with faculty colleagues, were always informed by a moral, philosophical, and learned
perspective. Read more >>
Professor Thomas Healy’s new book, “Soul City: Race, Equality, and the Lost Dream
of an American Utopia”, which explores the rise and fall of Soul City, a concept developed
and nurtured in the 1970s by civil rights leader Floyd McKissick, is receiving rave
reviews.
Seton Hall Law congratulates Craig Carpenito '00, who has joined King & Spalding as
a partner in the firm’s Special Matters and Government Investigations practice group
in the New York office. Mr. Carpenito has also joined the Seton Hall Law Board of
Visitors. Read more >>
On January 12, 2021, 157 Law School Deans from schools across the country published
a statement addressing the 2020 election and the events that took place in the United
States Capitol last week. The statement marks a rare occasion. It is unusual for such
a diverse group of law deans to come together to speak as one on an issue that falls
outside the ambit of legal education. Read more >>
Professor Jenny-Brooke Condon presented an argument before the New Jersey Supreme
Court challenging the State’s denial of unemployment benefits to an individual who
was detained on charges that were subsequently dismissed. Read more >>
During the Fall 2020 semester, faculty in the Seton Hall Law School Center for Social
Justice (“CSJ”) worked closely with law students researching the impact of COVID-19
on survivors of domestic violence in New Jersey in conjunction with the non-profit
organization Partners for Women and Justice (“Partners”). Read more >>
US Attorney Carpenito operationalized a vision for the office that positively impacted
the lives of the citizens of New Jersey, which he accomplished through significant
organizational change and strengthened relationships with state and city law enforcement.
Read more >>
Law Professor Paula Franzese has been named one of the "Top Women in Law" by the New
Jersey Law Journal. Considered "the statewide legal authority" of the New Jersey legal
community, the New Jersey Law Journal has been published since 1878. The award, which
was last bestowed in 2018, was through the submission of nomination letters and curricula
vitae and the deliberation of a panel. The criteria was "impact." There are more than
75,000 lawyers in New Jersey; twenty women were honored. Read more >>
As an extension of our past series on vaccines, Seton Hall University School of Law
Professor Carl Coleman discusses the ethical issues of COVID-19 vaccines challenge
trials with Dr. Bryan C. Pilkington of the School of Health and Medical Sciences at
Seton Hall University. Read more & listen to podcast >>
Professor Jennifer Oliva has been awarded the prestigious 2021 Health Law Community
Service Award for the AALS Law, Medicine and Health Care Section. The Section annually
gives an award to recognize outstanding contributions of law teachers in the service
of health law. The award is designed to recognize a wide variety of community service
activities, including pro bono litigation, legislative advocacy, consulting on public
initiatives, and other major projects. Through her extensive scholarship, grant work,
and public advocacy including amicus briefs, Professor Oliva has championed issues
of justice for people with opioid use disorder (and other substance issues) and for
veterans with disability issues. She has also focused her advocacy in the areas of
privacy rights and race implications of COVID-19 response efforts. Professor Oliva's
service to law students and to the community-at-large is admirable and extensively
described in the award announcement. She is a graduate of the United States Military
Academy at West Point, an Army combat veteran, and an honors graduate of the Georgetown
University Law Center. Read more >>
Seton Hall Law veterans enrich our community because they exemplify what it truly
means to give back. Their strength and selflessness inspire us to be better versions
of ourselves. This call is certainly a strong reason why they choose to pursue a legal
career – to serve generously again in the interests of transforming the lives of others
through the power of the law. November is National Veterans and Military Families
Month. As we take a moment to reflect on the blessings we have because of their sacrifice,
we realize the importance of telling their personal stories... Read more >>
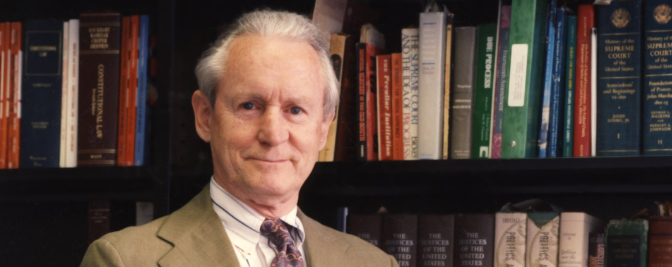
Professor Thomas Healy is a nationally renowned legal expert in the areas of constitutional
law, freedom of speech, legal history, civil rights, and federal courts. He is entering
his eighteenth-year teaching at Seton Hall Law. In addition to being a stellar teacher,
Healy’s background in journalism coupled with his passion for the law makes him one
of the most gifted legal scholars in the country. In his latest book, Soul City:
Race, Equality, and the Lost Dream of an American Utopia, Healy combines his passions
to tell the story of an attempt in the 1970s to create a city dedicated to the promise
of racial equality in the heart of Klan Country.
Are you a Veteran or Military-Affiliated student? Are you looking to pursue higher
education and want to hear how you can take advantage of the VA's Education Benefits.
Any Veteran or Military-Affiliated student who is interested in pursuing any type
of higher education degree should attend this virtual information session on November
11, 2020 (12:00–13:30 p.m.) Read more and register to attend virtual Information Session >>
This community conversation addressed the history of voting rights in this country,
including the ratification of the 14th Amendment, the passage of the Voting Rights
Act of 1965, and the Supreme Court’s recent decision in Shelby County v. Holder, where
the court struck down a formula at the heart of the 1965 Voting Rights Act.
On September 8th, 2020, the Seton Hall Law Asian Pacific American Law Students Association
(APALSA) hosted “Asian Americans at a Crossroads: COVID-19, #BLM, Discrimination,
and Allyship,” a virtual conversation featuring Queens College President Frank H.
Wu and moderated by Professor Marina Lao.
“The Human and Scientific Costs of the ‘China Initiative’” is the first of a series
of webinars to examine the ramifications of the U.S. Justice Department’s “China Initiative”
on the civil rights and security of Chinese Americans, Chinese immigrants, and Chinese
Nationals working in the U.S., as well as the consequences for the broader American
society. Read more >>
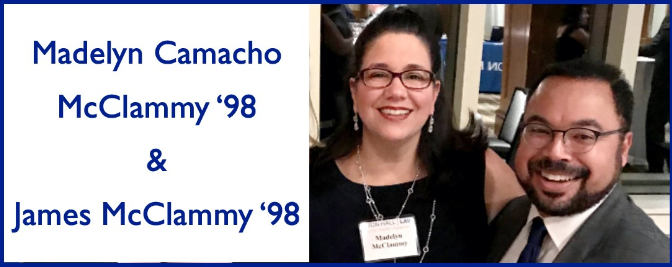
Many alumni children grow up as part of the Seton Hall Law network. For those inspired
to follow in their parents’ footsteps, it is no surprise that so many of them choose
Seton Hall Law because they know firsthand the caliber of the faculty and the honored
commitment of producing practice-ready lawyers. While Seton Hall Law has always been
a transformational place, its national reputation has grown, making it even more of
a draw for next generation lawyers. Read more >>
Class of 93 Alums Nancy Shore DiLella and Simone Handler Connect John DeFuria, 3L
Health Law Student with Remote Internship
Seton Hall Law hires Seton Hall Law. In the midst of the COVID-19 pandemic, the loyalty
of the Seton Hall Law community has remained steadfast in securing internship and
employment opportunities for students to gain practical hands-on experience, whether
remote or in-person. Read more >>
Kevin G. Walsh ’98 was appointed as the 123rd President of the Essex County Bar Association
(ECBA) on May 11, 2020. The Honorable Sallyanne Floria ’78, Assignment Judge in the
Essex County Vicinage, swore in Walsh. His appointment marks the third consecutive
appointment of a dynamic Seton Hall Law alum to hold the position – Matthew Schultz
’02 (2019-20), Raj Gadhok ’99 (2018-19), and Francine Aster ’87 (2017-18). Walsh Co-Chairs
the Government and Regulatory Affairs Department for Gibbons, P.C. and is a member
of the firm’s Executive Committee. Read more >>
Marc Larkins ’97 and Evelyn Padin ‘92 serve as the Co-Chairs of the Diverse Attorneys
of Seton Hall (DASH) Advisory Committee. The DASH Advisory Committee is comprised
of more than 25 alumni from various practice areas, geographic locations, and diverse
backgrounds with the goal to collaborate with Seton Hall Law on innovative ways to
enhance diversity, inclusion and equity initiatives.
We have lost a great legal mind who transformed the lives of many for the better by
virtue of her work has an attorney, law professor and Supreme Court Justice. May
you be inspired by her example and tenacity. Read more >>
The faculty in the Center for Health & Pharmaceutical Law continue to work closely
with law students who are researching COVID-19 topics. We are pleased to bring you
this ongoing series, which includes articles that the students have written based
on their research. In her fourth article, Jessica Kriegsfeld explores whether exemptions
are likely to be available if states mandate a COVID-19 vaccine once it is available
to be distributed. She consulted with Professor Angela Carmella and Professor Carl
Coleman on her research. Read full article >>
The first Seton Hall Law appointee to serve on the New Jersey Supreme Court is retiring.
Associate Justice Walter F. Timpone ’79 was sworn-in by Chief Justice Stuart Rabner
on June 2, 2016 at Seton Hall Law School, and has served the Court and the citizens
of New Jersey with honor and dignity. In November, Justice Timpone will reach the
mandatory retirement age. The New Jersey State Senate yesterday afternoon unanimously
confirmed Governor Phil Murphy’s nomination for Fabiana Pierre-Louis to succeed Justice
Timpone. Read more >>
Seton Hall Law’s Institute for Privacy Protection and Gibbons Institute of Law, Science
& Technology will host an online event on “Privacy and Intellectual Property in the
Age of Coronavirus” on September 17 from 12:00 -2:30 pm EST. Speakers will include
legal academics, practitioners, and government officials who will discuss the impact
of the COVID-19 pandemic on privacy and intellectual property. Read more & Register >>
Professor Richard Winchester explains executive order signed by President Donald J.
Trump on August 8, directing the government to defer a portion of the tax withheld
from the paychecks of certain workers. Legal challenges are expected. However, if
implemented, the measure would provide very limited relief while leaving workers with
a huge tax debt that they must pay at the end of the year. Read more >>
The faculty in the Center for Health & Pharmaceutical Law continue to work closely
with law students who are researching COVID-19 topics. We are pleased to bring you
this ongoing series, which includes articles that the students have written based
on their research. In her third article, Jessica Kriegsfeld explores whether the
government can mandate a COVID-19 vaccine once it is available to be distributed.
She consulted with Professor Carl Coleman, Professor Angela Carmella, and Professor
Jennifer Oliva on her research. Read more >>
“Michele has dedicated her career to establishing diverse, inclusive, and engaging
workplaces. She brings an unparalleled ability to create meaningful cultures and relationships
among employees by implementing policies that help people connect with one another
and embrace the power of diversity to improve business operations,” says Dean Kathleen
M. Boozang. “Major League Baseball did not just hire a Seton Hall Law alum. MLB hired
a stellar and accomplished advocate for equity, justice, and fairness. Read more >>
Many states have pandemic public health guidelines specifically for houses of worship,
including bans on singing during indoor services with occupancy limits. Yet, no other
indoor operations have similar bans. Seton Hall University School of Law Professor
Angela Carmella explores the relevant First Amendment issues related to public health
restrictions on churches. She also reviews the recent religious freedom litigation
related to COVID19, including several cases decided by the U.S. Supreme Court. Read more >>
The faculty in the Center for Health & Pharmaceutical Law has been working closely
with law students who are researching COVID-19 topics. Some students are also enrolled
in the course, COVID-19: Current Topics in Pandemic Law & Policy. We are pleased to
present this series, which includes articles that the students have written based
on their research. In her second article, Jessica Kriegsfeld explores who will pay
for the COVID-19 vaccine once it is available to be distributed. She consulted with
Professor Carl Coleman and Professor John Jacobi on her research. Read article >>
In the latest installment of the Center for Health & Pharmaceutical law's Ask a Compliance
Officer Series, Professor Jacob Elberg interviews Gary Giampetruzzi and Jane Yoon,
partners at Paul Hastings. The discussion focuses on how the ability to conduct investigations
has been impacted by COVID-19, and how this has evolved over the course of the pandemic.
They discuss navigating both restrictions and re-openings, which have varied widely
across locations. Other interview questions explore how to approach data collection
for investigations, how compliance resources have been reallocated and prioritized
in the current environment, and the expectations of government enforcers during recent
investigations. They also comment on impacts to compliance training and the current
opportunity for companies to focus on it. Read article >>
The faculty in the Center for Health & Pharmaceutical Law has been working closely
with law students who are researching COVID-19 topics. Some students are also enrolled
in the course, COVID-19: Current Topics in Pandemic Law & Policy. We are pleased to
present this series, which will include articles that the students have written based
on their research. In this first article, Jessica Kriegsfeld addresses the question
of which populations should be prioritized to receive a vaccine once it is approved
and available. She consulted with Professor Carl Coleman on her research. Read article >>
The Council on Foreign Relations has elected Seton Hall University School of Law Professor
Margaret K. Lewis to life membership. Professor Lewis has dedicated her legal career
to international law, human rights and criminal justice, specifically in China and
Taiwan. Read more >>
This week's COVID-related news includes proposed safety guidelines created by an advocacy
coalition seeking to preserve family presence at healthcare facilities during the
pandemic. While the U.S. government funded a leading vaccine candidate, the FDA
approved a test to quickly distinguish seasonal flu from COVID-19 and will soon be
reviewing a wearable device that can detect and monitor COVID infections. In other
health law news, the US Supreme Court ruled on a religious exemption to the Affordable
Care Act. For these updates and others, review our Health Law Weekly Roundup. Read more >>
Exciting and interesting wide-variety of topics were explored during weeks four and
five of Seton Hall’s newest course COVID-19: Current Topics in Pandemic Law and Policy.
Professor Jennifer D. Oliva's latest update on new course focused on privacy and telemedicine
and COVID-19 therapeutics and clinical trials. The class also discussed pandemic
impacts on small businesses, workers, labor laws, criminal, policing, and prisons.
Read more >>
The National Law Journal has released employment data for 2019 law school graduates,
Seton Hall Law remains one of the nation’s top law schools on this critical metric.
Seton Hall Law ranks #1 of more than 200 law schools in placing their 2019 graduates
into State & Local Clerkships, and #20 into Full-time law jobs. Read more >>
This summer is flying by at an alarming pace. This is the 2nd update on Seton Hall’s
newest course COVID-19: Current Topics in Pandemic Law and Policy and the class has
been absolutely terrific. Professor Jennifer D. Oliva provides an update and recommended
readings. Read more >>
This weekly roundup of health law news includes reporting on recent court decisions,
medical technology advancements related to vaccines, chemotherapy and other areas,
and new initiatives launched by the Department of Justice and the FDA. Read more >>
Even though we stopped driving, flying and going out during COVID-19 lockdowns, air
pollution did not decrease significantly. Professor Heather Payne examines the reasons
for this and explains why pollution might become worse than the pre-COVID period once
lockdowns are fully lifted. As decreases in air pollution can improve health outcomes,
Professor Payne also suggests areas of focus in decreasing pollution levels. Read more >>
Professor Heather Payne examines the environmental aspects of COVID-19. "We’ve learned
through this crisis that higher levels of air pollution lead to a higher level of
mortality from COVID-19. Specifically, a Harvard study concluded that “a small increase
in long-term exposure to PM2.5 leads to a large increase in the COVID-19 death rate.”
People who lived with long-term pollution exposure for 15-20 years had significantly
higher mortality rates." Read more >>
The Center for Health & Pharma Law at Seton Hall has compiled a weekly roundup of
interesting news articles related to health law. This week's summary is focused on
the pharmaceutical industry, the impact of COVID-19 on health and wellness, and medical
device innovations. Read more >>
Regina Gore Cavaliere, a long-time member of Seton Hall Law’s U.S. Healthcare Compliance
Certificate Program and Plus Program faculty, is currently the Chief Ethics and Compliance
Officer at Esperion. Seton Hall Law sat down with Regina to talk about emergent risks
and compliance strategies during the COVID-19 pandemic. Read more >>
The Healthcare Compliance Certificate Program is now offered in a new unique remote-learning
format that will continue to deliver the same content through a blend of thoughtful
expert presentations, case study analyses, offer opportunities to get to know fellow
participants, and earn a Compliance Certificate. Learn more >>
In Seton Hall Law’s newest course COVID-19: Current Topics in Pandemic Law and Policy, Prof. Jennifer Oliva’s students spent the first week of class discussing and analyzing
the book Pandemic by Sonia Shah, an award winning science journalist. The book draws
parallels between Cholera and newer pathogens like Ebola, coronaviruses and drug-resistant
superbugs. It emphasizes the cultural, social, and economic commonalities that have
characterized pandemics throughout human history. Read more >>
The arrest last month of a former Cleveland Clinic Foundation employee for allegedly
failing to disclose to the National Institutes of Health that he held positions at
universities in the People’s Republic of China (PRC) is the latest in a string of
cases under the Department of Justice’s “China Initiative.” Professor Margaret K.
Lewis examines case. Read more >>
Domenick Scrivanich, Class of ’21, overcame great personal hurdles to arrive at law
school two years ago. Now, sober for 7 years this November, Dom’s future holds hope
and promise. “I came to law school so that I could help addicts and alcoholics,” says
Dom. “I want to use my degree to do some good and hopefully positively affect the
lives of those still sick and suffering in a major way, whether it be through lobbying
or acting as general counsel for a large drug rehabilitation center.” Read more >>
Governor Phil Murphy nominated Fabiana Pierre-Louis, a graduate of Seton Hall Law
School’s Summer Institute for Pre-Legal Studies (Pre-Legal Program), and former United
States Attorney, to be the first African America woman to serve on the New Jersey
Supreme Court. “Seton Hall Law is thrilled Governor Murphy has nominated a graduate
of the Institute to be a member of the New Jersey Supreme Court for this historic
appointment,” said Dean Kathleen Boozang.
Three years ago, a group of extraordinary students walked across the front steps at
Seton Hall Law to begin their journey in becoming lawyers and joining the legal profession.
At a time when social distancing has become the new normal, students were invited
to the front steps of the law school (within a time slot) to take a few photos in
front of the building, where their journey began. Read more >>
In today's business environment, different fraud and corruption risks are emerging
in the virtual new normal. At the same time, compliance resources are under pressure
from a budgetary and time perspective, and individual employees may be under more
pressure to produce results, in combination with new personal struggles. Richard
Bistrong, CEO of Front-Line Anti-Bribery LLC, and a faculty member in the Seton Hall
Law Health Care Compliance Certificate Program, offers his perspective on the current
environment and suggested strategies for compliance leaders to influence and inspire
their front line colleagues. Read more >>
At a Senate Judiciary Committee hearing earlier this week, business leaders renewed
their calls for legislation shielding companies from lawsuits by employees or customers
infected with COVID-19. Professor Carl Coleman explains why broad immunity from liability
is a bad idea. Read more >>
In general, courts tend to defer to actions taken by state public health officials
to protect the public from infectious diseases, even if those actions place some limitations
on individual liberty. Broad claims that states lack the authority to prohibit non-essential
activities during a pandemic are therefore unlikely to be successful. However, some
state laws may be vulnerable to a variety of more narrowly drawn challenges. Professor
Coleman discusses key issues currently being litigated. Read more >>
New course focused on the legal aspects of the coronavirus pandemic. Set to begin
in just a few weeks, the course, COVID-19: Current Topics in Pandemic Law and Policy, is designed to prepare law students to tackle the complex law and policy problems
associated with the virus and the response to the pandemic. Throughout the seven-week
seminar, law students will examine the legal and ethical foundations of pandemic and
emergency preparedness, intervention, and evaluation in the context of the novel coronavirus,
SARS-CoV-2. Read more >>
Businesses that are not lucky enough to win the Payroll Protection Program lottery
can get some limited financial relief from another temporary program that was included
in the CARES Act. It’s called the Employee Retention Credit and it indirectly subsidizes
a portion of the wages that a business pays to its workers during the economic slowdown.
Professor Winchester provides answers to some key questions about that program. Read more >>
As the COVID-19 pandemic has forced social distancing and self-quarantining, schools
have had to wrestle with how they will satisfy their legal obligation to provide special
education services to students with disabilities from a distance. Professor Tara Ragone
explains. Read more >>
We're continuing our series where Seton Hall Law School’s Center for Health & Pharmaceutical
Law sits down with a life sciences compliance officer to find out what is top-of-mind
for him or her right now. Here is the next installment in this series, a conversation
with Richard Eschle. Read more >>
Professor Ndjuoh MehChu joined the Seton Hall Law faculty in July 2020. He teaches
in the areas of torts, civil rights, and critical race theory. Current research projects
bring to bear legal realist claims about the interplay of power and oppression to
explore the various ways institutions fail to implement rights-protective measures
for marginalized groups.
Professor Carl Coleman answers some basic questions about challenge studies and explains
how deliberately exposing healthy people to COVID-19 can be both scientifically useful
and ethically sound. Read more >>
Telemedicine is a tool that permits health care providers to virtually assess an individual’s
symptoms to develop a diagnosis and treatment plan as well as to monitor the patient’s
health. This is particularly important during the COVID-19 pandemic because use of
telemedicine alleviates the need for individuals to leave their homes to obtain health
care services. Instead, patients can use their telephones, computers, or tablets to
communicate with their treatment providers. Read more >>
We’re rolling out a new series where every week, Seton Hall Law School’s Center for
Health & Pharmaceutical Law will “sit down” (virtually, of course) with a life sciences
compliance officer to find out what is top-of-mind for him or her right now. Here
is the first installment in this series, a conversation with Michael R. Clarke. Read more >>
Wishing all Muslim members of the Seton Hall Law School family… “a generous Ramadan”…
Ramadan Kareem! Read More >>
Earlier this month, the New Jersey Department of Health released guidance for the
allocation of ventilators and other critical care resources during a public health
emergency. Professor Carl H. Coleman explains New Jersey’s Ventilator Allocation Guidelines.
Read more >>
Professor Richard Winchester joined the Seton Hall Law faculty at the beginning of
the 2018-19 semester with an expertise in small business and federal employment tax
policy.
Professor Richard Winchester provides in-depth information about different scenarios
related to receiving stimulus money. Read more >>
From early in the COVID-19 crisis, cybersecurity experts have warned about a rise
of social engineering attacks, such as phishing emails, spoofed websites impersonating
public health authorities such as the World Health Organization and the U.S. Centers
for Disease Control, and fake coronavirus mobile apps. Professor David Opderbeck examines
vulnerabilities and provides tips for practicing good cyber hygiene to flatten the
curve of cyber attacks. Read more >>
As part of the CARES Act, the federal government is issuing up to $1,200 to certain
individuals to help keep money in people’s pockets in the wake of the economic shutdown
precipitated by the coronavirus pandemic. Congress appointed the Internal Revenue
Service to distribute the money and directed the agency to pay eligible persons who
filed tax returns for either 2018 or 2019. Professor Richard Winchester answers questions
about the IRS Web Portal for Non-Filers. Read more >>
Efforts to develop treatments and, ultimately, a vaccine for COVID-19 center on the
successful design and implementation of clinical trials. To help you make sense of
developments in this area, we have put together a few questions and answers about
how clinical trials work. Professor Carl H. Coleman answers key questions about how
clinical trials work. Read more >>
Professor Jennifer D. Oliva briefly summarizes changed rules that pertain to Medicare-reimbursable
telemedicine health care treatment services in response to the COVID-19 pandemic,
as well as provides links to several primary source resources relevant to Medicare
telehealth treatment providers. Read more >>
Professor Carl H. Coleman answers five key questions for Healthcare Workers facing
the risk of infection. Read more >>
Adjunct Professor of Legal Practice, Ricardo (Rick) Little spent the majority of his
legal career at the New Jersey Attorney General’s Office. Professor Little also served
as the Executive Director of the New Jersey Transportation Trust Fund Authority and
the Director of the state’s Crime Victims Compensation Office. Read More >>
New Jersey hospitals are on the front lines in the fight against COVID-19. They have
experienced many struggles in the last several weeks, including shortages of ventilators
and PPEs, lack of day care for their workers’ children, and high levels of stress
for their careviers. One significant problem has now been addressed by Commissioner
Judy Persichilli of the New Jersey Department of health. Read more >>
With lives uprooted throughout the world due to COVID-19, Seton Hall Law faculty members
offer expert legal commentary on various issues. The below highlights professors addressing
the ongoing impacts of the pandemic. Read More >>
Roman Catholics together with many Christians of other denominations mark the week
which begins on Palm Sunday, April 5, as the most solemn week of the Church's faith
life. Lent officially ends on Wednesday. Holy Thursday, Good Friday and Easter Vigil
make up the so-called Triduum culminating in Easter Sunday. These are the Christian
"high holy days." Read More >>
Professor Ilya Beylin joined the Law School in July 2019. He comes to Seton Hall Law
as an expert in financial and business law. His scholarship combines legal analysis,
data driven observation, attention to institutional dynamics, economic theory and
pragmatism. Read More >>
During its annual Woman of Substance event on February 12, Seton Hall University School
of Law’s Women’s Law Forum honored three powerful women attorneys who exemplify leadership,
character, and achievement in the legal field. The Honorable Linda Lordi-Cavanaugh
’79, Mayling Blanco ’06, and June Forrest were recognized for inspiring young lawyers
and pursuing the ideals of justice and service. They each shared details of their
personal morals and beliefs that guided them into lucrative legal careers. Read More >>
Professor Jennifer Oliva joined the Law School in July 2019. She comes to Seton Hall
Law from West Virginia School of Law. She is a legal expert in health, FDA, and evidence
law. A graduate of the United States Military Academy, she was elected as a Rhodes
and Truman Scholar and was recently selected as the 2019 Ike Skelton Award Winner
by the Truman Scholarship Foundation and a 2019 Weit Life Science Law Scholar. Professor
Oliva is the 2019- 2020 Chair-Elect of the American Association of Law Schools Section
on Law and Mental Disability. Read More >>
Seton Hall University School of Law student, Stephanie L. Flackman ’20 was selected
as the first place winner of the ABA Health Law Section Law Student Writing Competition.
Flackman's paper, The Debilitating Disease of Chronic Pain and the Case for Mandated
Integration of Evidence-Based Alternatives into Individualized Treatment Plans will
be published in The Health Lawyer. Her paper was selected first among submissions
from students at ABA-accredited law schools across the nation. Read More >>
From NJBIZ: "Thanks to educational initiatives and technological advances, businesses
and individuals enjoy more protection than ever against cyberthreats. But criminals
are equally diligent about breaching those defenses, warn experts, who pointed out
some emerging and trending cybersecurity threats." Read More >>
Seton Hall University School of Law launched a new course this spring focused on the
trending subject of Data Analytics. The unique course material examines how statistics
and data can be used in real-world legal practice. Read More >>
Professor Deborah Schander joined Seton Hall Law in January 2019. She was named to
the newly inaugurated Center for Information and Technology, which houses the library,
Information Technology, Law Practice Technology, and Educational Technology. Read More >>
On February 8, 2020, the second year hybrid class was welcomed into Professor Paula Franzese's
home to celebrate the friendships and spirit of community that is a part of the Seton
Hall Law experience. More than 45 students and their family members enjoyed an Italian
feast. Under the leadership of classmates Elise Leonard and Maryam Hassimi, the class
raised $2,200 for the Law School's Public Interest Law Fellowships to submit the winning
bid for the Franzese penne alla vodka dinner at this year's Public Interest Auction.
Read More >>
From NJBIZ: With the advent of sports gambling in New Jersey, a raft of new rules
were promulgated to maintain the probity of the industry. In response, Seton Hall
University School of Law deans Kathleen Boozang, Tim Glynn, and Rosa Alves helped
organize a Gaming, Compliance and Integrity Boot Camp that the law school will host
from March 9 to March 11. Read More >>
Professors Michael and Lesley Risinger '03 and Seton Hall Law's Last Exoneration Project
recently gained statewide attention in the Star-Ledger, Bergen Record, WHYY, and NBC
New York for their appeal on behalf of two wrongfully convicted men for a double murder
that occurred in 1995. Their work with The Last Exoneration Project provided free
investigative and legal services to the innocent men.
In recognition of Black History Month, Seton Hall University School of Law is celebrating
alumni who have made a difference both in the black community and the legal profession.
In celebration of Black History Month, Seton Hall University School of Law is recognizing
three black students whom, for the first time in the school’s history, hold prominent
leadership positions simultaneously - Melissa Walker ’20 is President of the Student
Bar Association, Tatiana Laing ’20 is Editor-in-Chief of the SETON HALL LAW REVIEW,
and Ifedapo Benjamin ’20 is Editor-in-Chief of the SETON HALL LEGISLATIVE JOURNAL.
Professor Jacob Elberg joined Seton Hall Law in January 2019. Most recently, he was
an Assistant U.S. Attorney at the U.S. Attorney’s Office for the District of New Jersey,
specializes in Health Law, Health Care Fraud and Abuse, Evidence, and Data Analytics.
Read More >.
From January 6-17, 2020, select Seton Hall Law students immersed themselves in the
Denis F. McLaughlin Advanced Trial Advocacy Workshop - an intense two-week experience
for 16 of the Law School’s most committed trial advocacy students. Read More >>
Professor Karla Foy teaches Lawyering and serves as the Associate Director of the
Academic Success program. She has practiced Education Law in various contexts and
has managed and maintained a general law practice in Hackensack, New Jersey since
2005. Read More >>
Online web magazine, Slate, spoke to Seton Hall Law professor and expert in law and
technology, Gaia Bernstein on Google's recent announcement to increase privacy protection.
Read More >>
Seton Hall University School of Law proudly reports the third best pass rate among
New York law schools and the best pass rate among New Jersey law schools for the July
2019 Uniform Bar Exam, with a combined 94.26% or 115/122 first-time test takers passing.
Read more.
The Senate has confirmed Seton Hall Law alumnus, Marcus O. Hicks '03 to New Jersey
Governor Phil Murphy's Administration. Currently a member of the Cabinet, Hicks will
serve as the Commissioner of the New Jersey Department of Corrections. He has more
than 15 years of public policy and legal experience. Read More >>
Professor Brian Murray joined the Seton Hall Law faculty at the beginning of the 2018-19
semester. He most recently taught at Temple and is an expert in Criminal Law. Read More >>
After a nine-year career on active duty in the U.S. Army, Matthew Handley ’22 came
to Seton Hall Law School to learn how to make a deeper impact in his community and
to develop skills that would allow him to fight for social justice and systemic change,
particularly on behalf of his fellow veterans. “One of the ‘Core Values’ that you
are taught on your very first day in the Army is ‘Selfless Service.’ This was nothing
new to me, since I was taught the same thing by my parents growing up: that when you
see someone in need, you do whatever you can to help them.”
Sebastian Hernandez ’21 is a Colombian immigrant. He moved to the United States when
he was seven years old. “My first step on American soil was at Newark Airport. That’s
where my story in America began. However, my dad found a job in South Carolina, so
we settled in Beaufort County,” said Hernandez. Now he is back in Newark, NJ, motivated
to become an immigration attorney.
The intersection between the law and its real-world impact on families is what brought
Kerdesha Desir ’21 to Seton Hall Law School. Growing up in the Haitian and greater
Caribbean community, Desir witnessed that domestic violence was often mischaracterized
as simple “familial strife,” swept under a rug and never publicly discussed. “In our
culture, no matter how blatantly obvious the hardship of someone’s situation may be,
we are taught early on to address the issues within the family and not to get ‘outsiders’
involved,” said Desir.
"I can, I will. Watch me." Words that Joshua Copper '20 has lived by since he was
diagnosed with spinal muscular atrophy at just 18-months-old. Although he was "given
a body that doesn’t work the way I wanted it to," Cooper remains steadfast in serving
as an activist in and out of the classroom - and especially for those living with
disabilities.
From Washington Post: "One year after USA Gymnastics filed for bankruptcy in the face
of hundreds of lawsuits filed by girls and women sexually assaulted by former Olympic
team physician Larry Nassar, the legal fight over the organization’s money has yet
to produce a dollar for an abuse victim." Read More >>
Professor Heather Payne joined the Seton Hall Law faculty at the beginning of the
2018-19 semester. She came to Seton Hall Law from UNC and has unparalleled knowledge
of energy and environmental law. Read More >>
Christians perceive love in God’s creative will. Love is clearly the keynote of the
Christmas season, which begins the evening of December 24 and extends through January
12, the feast of the Baptism of the Lord. May your celebrations with family and friends
be filled with love and every joy of the season. And may you be energized for good
work in the days of the new year. Read More >>
Associate Clinical Professor at the Seton Hall Law's Center for Social Justice in
Kevin Kelly spoke with NJNN on the impact of short-term rental regulations impacting
Airbnb properties In Jersey City. He spoke of Airbnbs getting out of hand with individuals
initially renting out rooms in their house to make extra money to greedy developers
buying up properties, ultimately affecting rent-control regulations. Watch the interview >>
Seton Hall Law Professor Mark Denbeaux of the Center for Policy and Research appeared
on the Rachel Maddow Show on MSNBC discussing the report, "How America Tortures."
The report documents the U.S. Torture Program from the words of those who created
and approved the program as well as those who implemented it along with descriptions
of how it was implemented and applied. Watch the interview >>
Professor Michael Coenen joined the Seton Hall Law faculty at the beginning of the
2018-19 semester. Professor Coenen, who joined Seton Hall Law from LSU, is known nationally
as a Constitutional Law powerhouse. Read More >>
From New York Law Journal: Seton Hall University School of Law won the regional rounds
of the 70th annual National Moot Court Competition, held on Nov. 20-21 at the New
York City Bar Association. The winning team consisted of Sarah Ungeheuer, Samantha
Santola and Anthony Gingerelli. Read More >>
Professor Melanie Perez-Vellios is the Associate Director of Intro to Lawyering and
serves Fellows in the LEO program. Prior to joining Seton Hall Law, Professor Perez-Vellios
was Of Counsel to a mid-size New Jersey law firm specializing in employment and education
law. Read More >>
Seton Hall Law Professor Thomas Healy was published in the New York Times with his
op-ed, "The Unlikely Birth of Free Speech - Writing a century ago this weekend, Justice
Oliver Wendell Holmes Jr. created our modern understanding of the First Amendment,"
about the history of free speech in America. Read More >>
On Friday, November 1, the Seton Hall Law Review hosted a symposium honoring the extraordinary
work of Professor Charles A. Sullivan. The one-day event welcomed an auditorium full
of legal scholars from across the country reflecting upon Professor Sullivan’s scholarly
work and its profound impact. Four panels focused on a wide range of legal topics
reflecting Professor Sullivan’s scholarly interests. Read More >>
“As a professor and proud alumna of Seton Hall Law, I will continue to forge connections
among students, alumni, and the Law School community and emphasize to students that
they are part of a greater network of graduates and friends who seek to ensure their
success” explains Professor Pirone Palumbo. Read More >>
“When I became a student at Seton Hall Law over twenty years ago, I knew at the time
that I had joined an exceptional community of attorneys. My professors were instrumental
to my success and taught me valuable lessons that two decades later I plan to impart
to my first-year Lawyering students," says Professor Quaglia. Read More >>
Published by the American Health Lawyers Association (AHLA) in collaboration with
Seton Hall Law School’s Center for Health & Pharmaceutical Law & Policy, the second
edition of the Pharmaceutical and Medical Device Compliance Manual synthesizes what
can be an overwhelming quantity of authority into understandable analysis and practical
action for those who create, manage, and monitor effective life science compliance
programs in today’s complex enforcement and business environment. Read More >>
There was standing room only for the crowd in Seton Hall Law’s Larson Auditorium on
September 26 when the recently created Christie Institute for Public Policy held its
inaugural lecture. Cardinal Joseph W. Tobin C.Ss.R of the Archdiocese of Newark delivered
the invocation. Former New Jersey Gov. Chris Christie ’87 hosted New York Gov. Andrew
Cuomo for a discussion that highlighted the governors’ successful collaboration on
a range of issues confronting New York and New Jersey. Read More >>
Professor Katherine Moore is the founding director of the Health Justice Clinic in
the Center for Social Justice. She has expertise in disability law, health law, family
law, and poverty law. Previously Professor Moore served as an Acting Assistant Professor
at New York University School of Law and a staff attorney at The Bronx Defenders Family
Defense Practice. Read More >>
Paul B. Matey ’01 was sworn in as a Circuit Judge on the United States Court of Appeals
for the Third Circuit in March. Before donning the robe, Judge Matey was a partner
at Lowenstein Sandler, where he practiced complex commercial litigation and criminal
defense. He has also served as Senior Vice President, General Counsel and Secretary
at University Hospital in Newark, as well as Deputy Chief Counsel to New Jersey Governor
Chris Christie ’87, and Assistant United States Attorney for the District of New Jersey.
Read More >>
Seton Hall Law’s mission above all else is to provide an outstanding education. Coming
in a close second, our faculty aspires to positively impact law and policy through
research and law reform. We are growing again and that means we are hiring the next
generation of teachers and scholars who will perpetuate our mission. Fourteen new
faculty have joined Seton Hall Law over the last two years, embracing Seton Hall Law’s
ethos of One Student at a Time in and out of the classroom. Read More >>
The loyalty of the Seton Hall Lawyer is becoming the stuff of New Jersey lore. That
loyalty is best demonstrated by investments in the future that ensure continued access
to a Seton Hall Law degree, and the continued quality of the lawyer produced by Seton
Hall Law. Last year witnessed significant generosity by Seton Hall Law alumni, faculty,
and employees in gifts large and small. The gifts featured here evidence the incredible
intentionality of the donors about how they could best say thank you, and invest in
Seton Hall Law’s ability to continue to provide an outstanding education to our students.
Read More >>
Alessandra Masciandaro currently is a 3L in the Weekend Program for the 2019-2020
school year. She received her B.A. in Philosophy with high honors from Douglass College
of Rutgers University in 2007. After graduating, she found her way into a rewarding
career as a teacher. She continues to teach full time, while attending law school
on the weekends. Read More >>
Rachel Frost graduated from Seton Hall University in 2017 with a Bachelor of Science
in Business Administration- Marketing and Legal Studies. Rachel graduated summa cum
laude and class valedictorian with a 4.0 GPA from the Stillman School of Business.
As a law student at Seton Hall University School of Law, Rachel has engaged in a number
of internships and externships. Read More >>
Patricia Bergamasco is a third-year law student at Seton Hall Law for the 2019-2020
school year. She holds a Bachelor of Arts in International Studies from Ramapo College
of New Jersey. During her undergraduate studies, Patricia volunteered at a primary
school in her hometown where she assisted ESL students. Read More >>
Kyle Kennett is a third-year law student at Seton Hall Law for the 2019-2020 academic
year. Prior to attending law school, Kyle graduated from Rider University with a degree
in History and Secondary Education and was a substitute teacher in Kindergarten through
eighth grade. Since May of 2018, Kyle has worked as a law clerk at Santarcangelo Law,
L.L.C. in Montclair, NJ. Read More >>
Cardinal Joseph W. Tobin C.Ss.R conferred the St. Thomas More medal upon Kevin H.
Marino '84, Founding Partner, Marino Tortorella & Boyle, P.C. at the 35th Annual Red
Mass on September 20, 2019, at the Cathedral Basilica of the Sacred Heart in Newark,
NJ. Read More >>
I am thrilled to have joined Seton Hall Law’s faculty full-time in July 2019 after
almost a decade of practice as a corporate and financial markets attorney. As I gear
up to teach Business Associations and Securities Regulation in the coming year, I
am excited to leverage my practice experience in developing an onramp for students
into the world of business law. Read More >>
We want to assure you that the safety of Seton Hall Law School's water is a top priority.
The school, itself, and its water system are located outside of the affected Pequannock
area. As an extra safeguard, Seton Hall Law independently runs its own tests on water
in the building. Read More >>
preLaw's Back to School 2019 issue highlights Seton Hall Law as both a top school
in the Northeast with a rating of A- for practical training and A for Health Law.
Read more about these stellar rankings >>
From TIME: An Oklahoma judge ordered Johnson & Johnson to pay $572 million for its
role in the opioid crisis in a historic ruling on Monday, marking the first time an
opioid manufacturer has been deemed responsible in court and made to pay damages.
It could have implications for the slew of lawsuits filed against opioid manufacturers
and distributors throughout the country." Read Professor John Jacobi's comments on the issue >>
August 14-15, 2019 officially marked the beginning of the 2019-2020 academic year.
“You have put so much on the line to achieve the dream of becoming a lawyer – take
advantage of every opportunity.” - Dean Kathleen M. Boozang Read More >>
Seton Hall University School of Law is proud of its partnership with NJ Law and Education
Empowerment Project, better known as NJ LEEP, since its inception in 2006. This coming
fall, the Law School be welcoming two NJ LEEP students to its incoming class, Bashir
Herbert and Faatimah Jafiq.
Renowned evidence scholar, Seton Hall Law Professor D. Michael Risinger participates
in a six-part online symposium for the Washington Post on the use of forensics in
the criminal justice system. Read More >>
The Inaugural Faculty Fellow and Assistant Professor in the Institute for Privacy
Protection, Najarian Peters, has been named a Faculty Associate at the Berkman Klein
Center for Internet & Society at Harvard University for the 2019-2020 school year.
Read More >>
Professors John Jacobi, Jacob T. Elberg, Tara Adams Ragone, and Laura Hoffman represented
Seton Hall Law at the American Society of Law, Medicine & Ethics Annual Health Law
Professors Conference. The icing on the cake for Seton Hall Law was the bestowal of
an award for lifetime achievement on Professor Jacobi and the selection of Professor
Elberg as a promising new Health Law Scholar. Read More >>
The annual Above the Law Top 50 Law School rankings places Seton Hall Law at #35,
the fourth straight year Seton Hall Law ranks in its top 35. Read More >.
As originally published in Compliance Week - "Top Mind of Tomorow: 'Hope to pay it
forward'" - Editor’s note: Seton Hall Law student Hannah Levine was named CW’s first-ever
Top Mind of Tomorrow, and with it earned an invitation to attend our recently concluded
annual conference at Washington, D.C.’s Mayflower Hotel. In her own words, Hannah
describes her experience at the event. Read More >>
Seton Hall Law alumna, Cymetra M. Williams '15, will be awarded the Garden State Bar
Association's (GSBA) Young Lawyer Award on June 15 at its 44th Annual Scholarship
& Awards Gala. The GSBA is the largest and oldest organization for African-American
judges, lawyers, and law students in New Jersey.
Sarah (Hill) Rogerson ’03 was awarded the M. Shanara Gilbert Award by the Association
of American Law Schools’ Section on Clinical Education. The award recognizes her “commitment
to teaching and achieving social justice and providing legal services and access to
justice to those most in need.” Read More >>
Professors Solangel Maldonado, Amy Newcombe, and Charles Dewey Cole were celebrated
for their “valuable research and teaching contributions” to the Law School by Seton
Hall University’s Provost Office. Read More >>
After a three-year hiatus, Seton Hall Law is proud to publish three new articles in
the online student journal, Health Law Outlook. This student-run publication of Seton
Hall Law’s Health Law Forum, is an institutional eRepository showcasing the work of
students under one umbrella. Students explore current and emerging issues in scholarly
articles, through which they contribute to the rapidly evolving discourse in health
law and policy. Three recent graduates contributed to Volume 10, Issue 1. Read More >>
New Seton Hall Law Professor, Jennifer Oliva, expert in FDA, Health, and Evidence,
has been honored with the 2019 Ike Skelton Award by the Truman Scholarship Foundation.
The foundation memorializes President Harry Truman’s commitment to public service,
and recognizes those who answer the selfless call to public service. Read More >>
Seton Hall Law Class of 2019…we finally made it! Congratulations to all of you for
getting through this incredible challenge. Each of us had to sacrifice so much to
get to this day, and every time we thought we had sacrificed enough, we had to
dig a little deeper and give a little more. Read More >>
The racing world was jolted when, for the first time in its 145-year history, the
apparent winner of the Kentucky Derby, held on May 4, 2019, was disqualified for a
foul during the running of the race. Maximum Security dropped to 17th place after
stewards concluded he interfered with other horses. Apparent second-place finisher
Country House was declared the official winner, taking home the coveted title and
the winner’s purse. A new lawsuit, filed on May 14 in federal court in Kentucky on
behalf of Maximum Security’s owners by Dean Emeritus Ronald J. Riccio and Adjunct
Professor Dennis Drazin, seeks to reverse that reversal and restore the Derby roses
to Maximum Security. Read More >>
The National Law Journal has released employment data for 2018 law school graduates,
Seton Hall Law remains one of the nation’s top law schools on this critical metric.
Seton Hall Law ranks #11 of more than 200 law schools “in placing their 2018 graduates
into full-time, long-term law jobs that require passing the bar and were not funded
by the schools themselves—widely viewed as the gold standard for new lawyer employment.”
Read More >>
From the New Jersey Journal and New Jersey State Bar Association: When Evelyn Padin
stepped up to the microphone on stage at Union City High School to address local residents
in Spanish on a recent evening this month, the energy of the room cranked up to 11.
That’s because when Padin talks everyone listens. Read More >>
Seton Hall University School of Law is saddened by the death of Professor Emeritus
E. Judson Jennings who passed away in New York City on Wednesday, May 1, 2019 at the
age of 76. The building Seton Hall Law proudly calls home owes much to Professor Jennings,
who worked closely with Dean Emeritus Ronald Riccio on its design. Read More >>
Seton Hall is privileged to have among its faculty Professor Marina Lao, one of the
foremost antitrust scholars in the country. She has not only published on a wide variety
of antitrust topics over a long and distinguished academic career but has also helped
shape competition policies as the Director of the Office of Policy Planning at the
U.S. Federal Trade Commission while on leave from Seton Hall.
A 13-year-old girl sits in the backseat of the family car snapping selfie after selfie.
She's in constant motion, trying on pouts and smiles, tilting her phone high and low,
whipping her hair in all directions. Her dad fins the whole thing pretty funny, so
he records it on his phone and posts the video to Facebook and YouTube. Soon it's
spread across the internet, racking up millions of views and hundreds of comments.
Eventually it even plays on Good Morning America. In all that sharing, was the daughter's
privacy violated? And do we have an obligation to ask people before we spread their
image around the internet? According to a class of fifth-graders at the Montclair
Cooperative School in Montclair, New Jersey, the answer in both questions in a strong
"yes." Read More >>
TaxProf Blog ranks Seton Hall Law #22 on their annual list of 2019 Law School Rankings
by Employment Outcomes. The ranks come as a result of all data from ABA employment
reports. From TaxProf Blog: “The technique used incorporates each outcome with a unique
weight, rather than simply counting "good" and "bad" outcomes. In fact, this technique
does not rely at all on a subjective determination of what outcomes are good or bad.
It's an unsupervised machine learning technique that determines the weight of each
outcome based on its relationship to other outcomes among the 201 schools. Therefore,
this is a truly objective ranking measure.” Read More >>
On May 2, Seton Hall Law's Center for Social Justice was honored at ACLU of NJ's Lights
of Liberty Awards Dinner for its work with Paul Weiss and the Pro Bono Network.
Seton Hall Law Senior Associate Dean and Andrea J. Catania Endowed Professor of Law,
Timothy Glynn, spoke with Compliance Week about the skills needed for those in a Chief
Compliance Officer role. "Compliance officers should check out a new survey that reveals
the specific credentials and skills that companies are seeking today when making compliance-related
hiring decisions. One key finding from the survey, conducted jointly by Compliance
Week and the Seton Hall School of Law, is that most firms seek a broad range of leadership
skills in a compliance officer." Read More >>
"Getting shots in no fun. But it’s even less fun not to get them. Just ask Ethan Lindenberger,
a high school senior from Norwalk, Ohio. By age 18, kids are supposed to have received
shots for 16 different diseases. He'd only had shots for one or two. Why? His mother
believes that vaccines are linked to the developmental disorder autism — even though
that's not true." Read More >>
For decades, even as the Department of Justice has pressed for corporate cooperation
and self-disclosure, the health care industry and the white-collar defense bar have
expressed skepticism regarding the actual impact of engaging in those behaviors. When
it comes to the resolution of civil False Claims Act (FCA) cases – the primary tool
for government action in response to corporate misconduct in the health care industry,
through which the Department of Justice generates more than $2 billion annually –
DOJ’s response has been a series of public statements amounting to, “trust us, we
reward those things.” Read More >.
On April 8, 2019, Seton Hall University School of Law hosted the 2019 Hobbs-Larson
Lecture featuring Keynote Speaker Chief Justice Stuart Rabner of the New Jersey Supreme
Court. Chief Justice Rabner noted the importance of being “a catalyst for change”
as he guided an in-depth discussion into New Jersey’s criminal justice reform efforts.
Read More >>
In recent weeks, International Law activities at Seton Hall Law have been at the forefront.
Distinguished Practitioner in International Law, Dawn Yamane Hewett, presented a lecture
on “The Global Fight Against Corruption”; Students represented Seton Hall Law at the
International Chamber of Commerce Commercial Mediation and Jessup International Law
Moot Court competitions; Seton Hall Law hosted the 2019 ASIL International Organizations
Interest Group Works-in-Progress Workshop; and Katherine Comly ’20 was selected as
the recipient of the Summer International Law Fellowship for her internship at Global
Justice Center this coming summer.
For most of the 20th century, dads who wanted to share custody of their children after
a divorce were out of luck. “The way that custody is evaluated by courts has changed
over the decades, and the cases in which the mother had sole custody instead of the
father… that has changed drastically,” says Kevin Kelly, an associate law professor
at Seton Hall University’s Family Law Clinic. Read More >>
In November 2018, Susan Smalley ’18 was named Chief U.S. Probation Officer for the
District of New Jersey – the first woman in New Jersey to hold the position, and the
first Asian-American woman to hold such a position in the country. Capping a 26-year
career in federal service, the promotion is especially impressive since Smalley earned
her law degree later in life, beginning her J.D. studies in 2014 once her children
were teenagers.
Seton Hall Law will be holding its Annual Alumni Gala on May 10, 2019. The Public
Servant Award will be presented to The Honorable Michael Shipp '94, U.S. District
Court for the District of New Jersey; the Distinguished Graduate Award will be presented
to Lynn Fontaine Newsome '81, Partner, Newsome O'Donnell and Chair of the Seton Hall
Law Board of Visitors; and the Exemplary Service Award will be presented to Michele
Meyer-Shipp '95, Principal and Chief Diversity & Inclusion Officer, KPMG.
A judicial clerkship involves legal research and writing and is a great job for recent
law school graduates. Though a clerkship typically only lasts a year or two, it can
catapult young lawyers into prominent positions and become the foundation of a successful
career. While becoming a judicial clerk is no easy task, graduates of some law schools
are more likely to obtain a clerkship than their peers at other law schools. Here
are the 10 schools where graduates are most likely to become clerks, including the
percent of those in federal and state or local clerkships. Read More >>
We are reaching a tipping point moment for our democracy. Intolerance and incivility
are manifesting in alarming ways. Virtual mobs rush to judgment and use insult, ridicule
and shaming to silence and shun. Cyber sphere venom spills over into physical realms,
with incidents of hate crimes on the rise. With so much that is wrong, optimism can
seem naïve or even delusional. Except that conditional optimism is neither. Read More >>
The US Department of Justice has launched an investigation into the sales and marketing
of a drug approved three years ago to help treat Parkinson's patients suffering from
debilitating psychosis. Former DOJ attorney and Seton Hall Law Professor Jacob T.
Elberg weighs in.
The Seton Hall Law School Mock Trial team recently received the Best Cross Examination
team award and Third place overall in the regional National Black Law Student Association
Constance Baker Motley Mock Trial Competition in New Hampshire. The team looks forward
to competing again this time in Little Rock, Arkansas at the National Convention March
12-16, 2019.
Based on recent statements, the U.S. Department of Justice seems poised to provide
much needed guidance regarding the manner and extent of corporate cooperation credit
in False Claims Act cases. Examination of newly available data, however, demonstrates
that more wide-ranging, structural changes are necessary: The data raises substantial
questions not only about the credit given for cooperation, but about what the DOJ
values
in resolving FCA cases and whether there is appropriate consistency for cases handled
by
U.S. attorneys' offices across the country.
Pina Cirillo and Iman Saad are both new on the job at their respective employers,
but they’re not wasting time finding the office supplies and coffee maker. Both are
on the front lines of immigration law, meeting with detainees at Essex County Jail
and the Elizabeth Detention Center to offer pro bono representation through the Murphy
administration’s Detention and Deportation Defense Initiative. Read More >>
Over nearly five decades at Seton Hall Law, Professor Michael Ambrosio has inspired
the lawyer unique to Seton Hall Law — one who integrates jurisprudence into the everyday
practice of law and whose thinking is grounded in a Catholic view of justice. Read More >>
On January 31, Dean Kristen Boon spoke at the United Nations on how the law concerning
the international responsibility of states applies where a state or one of its organs
is involved or complicit in slavery.
Social Justice has been a motivating factor for most major life decisions for Tatiana
Laing ’20 since she moved to Washington D.C. for college in 2012. “Being an African
American woman in the most politically active city in the country at a time that included
the death of Trayvon Martin, Tamir Rice, Michael Brown, Freddy Gray and more, made
it nearly impossible for me not to become active in the Black Lives Matter Movement,”
said Laing. As a student activist, she helped create a racial justice organization
on her campus and together with her peers, lead the students in demonstrations, protests,
and teach-ins. Read More >>
Passions for service and social justice are what have brought Angelica Mercado ’21
to Seton Hall Law to pursue a career in service to her community. Coming from a family
of public servants and being a native of Newark, Mercado has been actively engaged
in the community since childhood through community service and volunteering. Read More >>
Hafsa Mansoor ‘20 came to law school to learn how to use the law to dismantle structural
violence, empower the silenced, and restore dignity to the marginalized. In particular,
Hafsa Mansoor is passionate about rectifying institutional inequities impacting women
of color. Read More >>
Anna Magallanes, a Seton Hall Law 3L, is making her mark in the Hispanic National
Bar Association. Originally from California, she arrived at Seton Hall Law as a nontraditional
student. What she initially thought would be only a two-year break between college
and law school turned into a decade, during which she gained invaluable experience
working for private and nonprofit immigration firms. Read More >>
On January 18, 2019, Seton Hall Law School held the Dedication Ceremony and Ribbon
Cutting for the reimagined DeCotiis Law Moot Courtroom. Replacing the original venue,
the new courtroom reflects state-of-the-art upgrades for the current generation of
advocates while symbolizing the dignity and transparency of the law for all those
who enter the Law School. Read More >>
Family. Education. Helping Others. Three core values that define Donald B. Hannon,
Sr. and that he has instilled in his family. Brianna Kostecka ’10, along with her
sister, Kerry Kostecka, and cousin, Donald Hannon, III, grew up with encouragement
and support from their family and especially their grandfather, Donald, Sr. Read More >>
Seton Hall Law Professor Margaret Lewis, expert on law in mainland China and Taiwan
with an emphasis on criminal justice, was, was quoted in several articles after a
Chinese court sentenced a Canadian man to the death penalty. Read More >.
Seton Hall Law Professor Stephen Lubben commented to the Financial Times on the recent
collapse of Sears, the risks, and costs involved. Read More >>
Lorraine Gerson, an assistant U.S. attorney in Newark who was the nation’s oldest-serving federal
prosecutor, died Monday at age 89. Gerson, who handled financial crimes and fraud
cases for four decades at the U.S. Attorney’s Office, kept on working far past the
age when most other people retire. Although she took leave late in 2018 to battle
cancer, U.S. Attorney Craig Carpenito said Gerson prosecuted more defendants for the
year than most other assistant U.S. attorneys in the office. Read More >>
In December 2018, John Jacobi, Seton Hall Law Professor of Health, Law and Policy
joined Steve Adubato for an interview on State of Affairs. As part of the Future of
Healthcare series, they discussed issues with getting access to appropriate care;
problems within the Medicaid system and the state’s regulatory structure to treat
mental and substance abuse disorders in a primary care setting. Read More >>
David Marella '15 has been named to Forbes 30 Under 30 Law & Policy list. In 2017,
the Trump administration's declared a state of emergency on the Opioid Epidemic; behind
the scenes was David Marella, a 29-year-old lawyer who managed the senior staff on
the White House team. Since the task force, Marella has returned to corporate law
at Gibbons PC. Read More >>
David Marella '15 has been named to Forbes 30 Under 30 Law & Policy list. In 2017,
the Trump administration's declared a state of emergency on the Opioid Epidemic; behind
the scenes was David Marella, a 29-year-old lawyer who managed the senior staff on
the White House team. Since the task force, Marella has returned to corporate law
at Gibbons PC. Read More >>
John J. Gibbons was born in Newark, and worked here for decades as lawyer, judge,
and law professor. His name graces the Newark skyline in a tribute both fitting and
ironic: fitting for his long and deep dedication to the city, and ironic for such
a quiet, humble man. In the 1950’s, he began working for the firm that now bears his
name. Read More >>
May your celebrations with family and friends be filled with love and every joy of
the season. And may you be energized for good work in the days of the new year. Read More >>
From the moment he met his first-year section, James McClammy ’98 felt a special bond
with his classmates and Seton Hall Law. The Class of 1998’s universal drive to succeed
was clear from their first day and is evident once again as they establish the Class
of 1998 Endowed Scholarship fund in honor of their 20 year reunion. Read More >>
On October 25, Seton Hall Law and Mayer Brown LLP were pleased to present the annual
“Hot Topics in Life Sciences Law” Symposium. With over 100 industry professionals
in attendance, the symposium explored emerging issues and legal trends impacting the
life sciences industry. Read More >>
Kathleen Boozang, dean of Seton Hall University School of Law since 2015 and a member
of law school leadership long before that, oversaw an increase in starting J.D. class
size from about 150 to about 250—in an era when overall demand for legal education
has wavered. Boozang over the years has held positions at Seton Hall Law that have
required to tackle a variety of issues. Read More >>
The Senate Judiciary Committee has passed bipartisan legislation sponsored by Senator
Joe Pennacchio and Senator Shirley Turner to create a commission that would develop
reforms and aid those who have been wrongfully convicted in New Jersey. Lesley Risinger,
Director of The Last Resort Exoneration Project at Seton Hall Law, advocated at a
committee hearing on October 29th. Read More >>
On October 22, 2018, Seton Hall University School of Law and Porzio, Bromberg & Newman,
P.C. hosted the 2018 Diversity Speaks Lecture Series featuring New Jersey Attorney
General Gurbir Grewal. Introduced by Dean Kathleen Boozang as a “man of integrity,”
General Grewal spoke of his Office’s pursuit of justice across a range of social issues,
including strengthening community relations with the state’s 35,000 law enforcement
officers and a multi-pronged effort to combat the opioid epidemic. Read More >>
A Seton Hall University School of Law professor and director of the Health & Pharmceutical
Law & Policy Program, Jacobi's reach extends beyond the classroom and into the hub
of state health care policy. There are several people who have cited his work, or
sought his expertise, on health care issues, most importantly on public health and
mental health - the latter which is taking center stage in the state.
As both a first generation college and law student, Steve McManus ’90 understands
the financing difficulties and challenges facing many students pursuing advanced degrees.
While attending Seton Hall Law in the evenings, Steve worked in a State Farm branch
office in order to support his dream of earning a law degree. Steve credits his Seton
Hall Law education and experience as a springboard to his personal career success.
Today, Steve serves as Senior Vice President and General Counsel at State Farm Insurance
Companies in Bloomington, Illinois. Read More >>
The New Jersey Law Journal has named Seton Hall University School of Law Dean Kathleen
M. Boozang to its list of the Top Women in the Law 2018. Dean Boozang was selected
as among “female attorneys who have influenced the law and legal profession in exceptional
ways over the last two years.” Read More >>
Highlighted in Seton Hall Law's 2018 Alumni Magazine, these five women alumnae have
set standards and made strides in the legal field. Click to read more about Margaret
Brinig ’73, Judge Katharine S. Hayden ’75, Paulette Brown ’76, Lynn Fontaine Newsome
’81, and Karol Corbin Walker ’86 Read More >>
On October 19 the Institute for Privacy Protection at Seton Hall Law will host a workshop
on Kids' Technology Over-Use. It will convene experts in the areas of technology design,
corporate activism, mental health, education, public advocacy and law to address kids'
excessive use of technology.
Seton Hall Law School kicked off the 2018-19 school year by conferring the Miriam
T. Rooney Medal on John V. Jacobi, Dorothea Dix Professor of Health Law & Policy and
Faculty Director of the Center for Health & Pharmaceutical Law & Policy. Senior Associate
Dean Charles Sullivan described the award as “a life-time achievement, all-around-athlete
award that recognizes not just professional accomplishments but character.” Read More
On November 2, 2018 the Center for Health & Pharmaceutical Law & Policy and Seton
Hall Law Review presents Race and the Opioid Crisis: History and Lessons. Recent responses
to the opioid crisis have drawn praise as drawing on public health principles. It
is concerning, however, that this public health-oriented response arises at a time
when the public face of opioid addiction tends to be white, while the public response
skewed toward criminal justice when the face of opioid addiction was seen as black
or brown.
Amy Gopinathan was a Student Fellow for the 2018-2019 academic year. She received
her A.B. in history with a concentration in the Near East and a certificate in Creative
Writing from Princeton University in 2014. After graduating, she worked as a tutor
and spent time researching and assisting on creative projects. Read More
Angela Cooper was a Student Fellow for the 2018-2019 academic year. Angela received
her B.A. in Communications with a minor in Political Science. Then she joined Teach
for America, where she taught at Academia De Niños. Read More >>
Shannon Finnegan was a Student Fellow for the 2018-2019 academic year. Shannon majored
in Communication at Fairfield University and minored in Catholic Studies and Italian.
She graduated summa cum laude in 2014. After college, she worked as a Contract Administrator
for an Educational Technology Group at Scholastic acquired by Houghton Mifflin Harcourt.
Read More >>
Seton Hall Law alumnus Steven Llanes ’13 was one of 59 individuals selected nationally
for the 2018 Presidential Leadership Scholars (PLS) program, a unique opportunity
for a group of high-potential leaders from across the United States to collaborate
and learn about leadership through studying the presidencies of George W. Bush, William
J. Clinton, George H.W. Bush, and Lyndon B. Johnson. Read More >>
New Jersey should now turn to reforming the laws that impose a cascade of court fines
and permit the suspension of hundreds of thousands of driver’s licenses each year
simply because of residents’ inability to pay justice-related debt. Read More >>
Joining the Law School’s administration this year are Professors Kristen E. Boon and
Brian Sheppard, who have been named as associate deans by Dean Kathleen M. Boozang.
“Both are outstanding classroom professors and productive scholars,” said Boozang,
“and I know they will bring the same enthusiasm and creativity to their new roles.”
Read More
Web-based apps and devices have transformed our students’ lives, creating new privacy
risks and changing ways of social interaction. In this edWebinar, Gaia Bernstein and
Jari Peters, professors at Seton Hall Law School’s Institute for Privacy Protection
in New Jersey, will present a new program that targets kids in fifth and sixth grades—the
ages at which they receive their first cellphones. The free program is unique in that
it includes both a curriculum for elementary and middle school students and lectures
for parents.
"Professor McQuade embodied what it meant to be a law professor at a Catholic law
school. We were blessed that he was so instrumental in Seton Hall Law’s formative
years. Frank also made his unique mark in New Jersey government. He was so proud
of Seton Hall University, New Jersey, and his home town, as evidenced by his “Essex1”
license plate! Always good-humored, he loved to engage about his many enthusiasms,
most especially his wonderful wife Theresa. He is missed." - Dean Kathleen M. Boozang
Read More >>
From June 11-14, 2018, Seton Hall Law held its bi-annual U.S. Healthcare Compliance
Certification Program (HCCP) and introduced its first HCCP PLUS on June 15. The traditional
multi-day event brought together industry leaders in compliance, ethics, health care,
regulatory, medical affairs, and legal to learn about compliance statutes and regulations,
as well as how to create a culture of compliance. Read More
Seton Hall Law invites interested applicants, admitted students and their families
to experience a day on campus with personalized visits to our Newark location. Plan
your visit around info sessions, classroom tours and other interests guided by current
students and faculty. Attend an info session
On May 19, 1991 Susan Iovine ’91 gave birth to her first son. Shortly thereafter,
she was studying for her Professional Responsibility final from her hospital bed.
And just 11 days after Luke Iovine, IV was born, she walked across the stage, newborn
in her arms, to graduate from Seton Hall Law.
Fast forward 27 years later to May 24, 2018, and Susan was once again on stage at
a Seton Hall Law’s graduation, this time with Luke’s father, Luke Iovine, III ’90
to hand their son, Luke IV his own Seton Hall Law diploma. Read More
You asked for deeper coverage on hot topics and more case studies, and we listened!
Join Seton Hall Law School faculty and respected industry leaders on June 15th for
an advanced supplement to the extraordinarily popular U.S. Healthcare Compliance Certification
Program, covering emergent issues in life sciences relating to prescription drugs
and medical devices. Register now!
"In a world that is governed by the rule of law, always try to reconcile law with love
and justice with mercy. Here is where service fits in – that by the work of our hands
we consistently recognize and respect the dignity, worth and rights of the human person." Read full keynote address.
Professor Paula Franzese featured on "Issues and Ideas" podcast
Seton Hall Law Professor Paula Franzese was featured on Chris DeBello's podcast "Issues
& Ideas" discussing evictions in New Jersey, how the court system favors landlords,
and pending legislation seeking to remedy the current system. Listen Now
Call for Jessup Moot Court Coach Applications
Seton Hall Law is seeking applications for a Co-Coach of the Jessup International
Law Moot Court Team. Applicants should have substantive knowledge of international
law as well as experience in persuasion and advocacy. Interested? Apply by May 25th!
Seton Hall Law Alum, John E. Keefe, Jr. '90, Sworn In As NJSBA President
Seton Hall Law alumnus, John E. Keefe Jr. '90, will be sworn in as the New Jersey
State Bar Association President on May 17, 2018 during the NJSBA Annual Meeting and
Convention. Read More >>
Seton Hall Law is Pleased to Have Honored Three Graduates at 2018 Alumni Gala
On May 11, 2018, Seton Hall Law honored The Honorable Madeline Cox Arleo '89 with
the Public Servant Award, Thomas P. Scrivo '89 with the Distinguished Graduate Award,
and Ricardo Solano, Jr. '98 with the Exemplary Service Award. Watch the Honoree Videos >>
Seton Hall Law Dean, Kathleen Boozang, Featured in US News - How to Answer Tough Law
School Interview Questions
While the majority of Seton Hall Law applicants are not interviewed, Dean Kathleen
M. Boozang spoke with US News about some of the questions she asks and the importance
of the responses. Law school admissions committees strive to identify students who
have the potential to have a lasting positive impact on the legal profession. That's
one reason why they look for applicants who have the capacity to speak with authority
and conviction in a way that inspires others. But law schools also have a more pragmatic
reason to recruit students with a silver tongue: Oral advocacy is a crucial part of
many legal jobs. Read More >>
District Court Names Seton Hall Law Alum U.S. Attorney for N.J.
Seton Hall Law alumni, Craig Carpenito '00 named by the United States District Court
as United States Attorney for the District of New Jersey. Read More >>
Seton Hall Law's Institute for Privacy Protection Featured on CBS This Morning
Fifth and six grade students in the NJ/NY area are learning about privacy before it
is too late thanks to Seton Hall Law's Institute for Privacy Protection's School Outreach
Program. It was recently featured on CBS This Morning where students are taught to
be mindful of their behaviors online, to make responsible choices, and to remember
that overusing can lead to oversharing. Read More >>
National Law Journal Ranks Seton Hall Law #17 in the Nation for Employment
The National Law Journal recently released employment data for 2017 law school graduates,
Seton Hall Law remains one of the nation’s top law schools on this critical metric.
Seton Hall Law ranks #17 of more than 200 law schools “in placing their 2017 graduates
into fulltime, long-term law jobs that require passing the bar and were not funded
by the schools themselves—widely viewed as the gold standard for new lawyer employment.”
Read More >>
Seton Hall Law Associate Dean Charles Sullivan Talks Equal Pay Bill Signing
On April 24, 2018, NJ Governor Phil Murphy signed into law a bill promoting equal
pay regardless of gender or race. Seton Hall Law Professor and Senior Associate Dean
of Faculty & Finance, Charles Sullivan spoke with ROI-NJ and Law360 as a legal employment
expert on the topic. Read More >>
Thomas P. Scrivo '89 to Receive Seton Hall Law's Distinguished Graduate Award at Its
2018 Alumni Gala
Seton Hall Law will honor Thomas P. Scrivo '89 with the Distinguished Graduate Award
at its annual Alumni Gala on May 11th. He vividly remembers his first days at the
Law School: “Seton Hall Law was very welcoming, and I instantly identified with everyone
walking the halls,” Scrivo recalls. “I get the same feeling when I come back today.”
Read More >>
Former Scholarship Recipient Gives Back
A scholarship recipient herself, Seton Hall Law alumna, Caitlin Petry Cascino ’12,
well understood the profound impact of scholarships on students’ lives. She and her
husband, Jordan, a 2011 M.A. alumnus of Seton Hall, are proud to be able to fund The
Caitlin P. ’12 and Jordan Cascino Annual Scholarship to enable deserving students
to obtain a legal education. Read More >>
President Nominates Seton Hall Law Alumnus Paul B. Matey to the Third Circuit
Filling the first of three vacancies in the Third Circuit Court of Appeals, President
Donald J. Trump announced his intent to nominate Seton Hall Law alumnus, Paul B. Matey
’01. Mr. Matey is currently part of the Executive Leadership team at University Hospital
in Newark serving as Senior Vice President, General Counsel and Secretary. Read More >>
Seton Hall Law's School Outreach Program Featured in Washington Post
The fifth-graders of Yolanda Bromfield’s digital-privacy class had just finished their
lesson on online-offline balance when she asked them a tough question: How would
they act when they left school and reentered a world of prying websites, addictive
phones and online scams?
Susan, a 10-year-old in pink sneakers who likes YouTube and the mobile game “Piano
Tiles 2,” quietly raised her hand. “I will make sure that I don’t tell nobody my personal
stuff,” she said, “and be offline for at least two hours every night.” Read More >>
The Honorable Madeline Cox Arleo '89 to Receive Seton Hall Law's Public Servant Award
at Its 2018 Alumni Gala
Described as deeply committed and passionate by her family, friends, and colleagues,
The Honorable Madeline Cox Arleo ’89 is this year’s Public Servant honoree. She will
receive the award at the Seton Hall Law’s Annual Alumni Gala on May 11th. Judge Arleo
has always had a lively interest in the criminal justice system having come from a
of law enforcement family. And there was “no question” she would attend Seton Hall
Law when she graduated from college. Read More >>
Meet Vanessa Pinto ’19: Center for Social Justice Scholar
Commitment to social change. Focus on providing legal services to those in need. Perseverance
in the face of great odds. These are the characteristics that define a Center for
Social Justice (CSJ) Scholar. Journalism helped lead Vanessa Pinto ’19 to her path
as a CSJ Scholar. Pinto attended Rutgers University and double majored in Political
Science and Journalism and Media Studies where she was involved with the Puerto Rican
Action Board and she tutored English for New Brunswick’s elementary school students.
Read More >>
Meet Arrianna Diamantis ’19: Center for Social Justice Scholar
Commitment to social change. Focus on providing legal services to those in need. Perseverance
in the face of great odds. These are the characteristics that define a Center for
Social Justice (CSJ) Scholar. Arrianna Diamantis ’19 has long been interested in the
criminal justice system. She grew up with one immigrant parent in a family that struggled
with finances. This exposed Diamantis to challenges that built in her a deep commitment
to helping the indigent, incarcerated youth, and those struggling to get by, and this
ultimately led her to pursue a career in law. Read More >>
Meet Omar Debs ‘19: CENTER FOR SOCIAL JUSTICE SCHOLAR
Commitment to social change. Focus on providing legal services to those in need.
Perseverance in the face of great odds. These are the characteristics that define
a Center for Social Justice (CSJ) Scholar. Omar Debs ‘19, a CSJ Scholar, comes from
an immigrant family that struggled for many years to build a life in the United States.
His family was impacted by issues such as immigration/deportation, poverty, and housing.
Read More >>
May 16 event - The Color of Law and How to End Segregation and Advance Fair Housing
in NJ
On Wednesday, May 16, 2018, Monarch Housing Associates in partnership with Seton Hall
University Law School, the Anti-Poverty Network of NJ, and NJ Institute for Social
Justice will host a Public Policy Forum on The Color of Law. The Public Policy Forum
keynote speaker and author Richard Rothstein will present the national research in
his book, The Color of Law: A Forgotten History of How Government Segregated America,
and take questions from the audience. Read More >>
Seton Hall Law Deans Write Op Ed for NJ Spotlight
Deans Charles Sullivan and Timothy Glynn wrote an Op Ed "A Call to Restore the Courts'
Role in Addressing Sexual Misconduct" for NJ Spotlight. The attorneys general of all
50 states, the District of Columbia, and several territories recently signed a letter
to Congress urging an end to mandatory arbitration of employment sexual harassment
claims. Read More >>
Ricardo Solano Jr. '98 to Receive the Exemplary Service Award at 2018 Alumni Gala
On May 11, 2018, Seton Hall Law will honor Ricardo Solano Jr. '98 with the Exemplary
Service Award at its annual Alumni Gala. Solano is a remarkable success story. Growing
up in inner city Paterson in a low income family raised by a single mom, he studied
philosophy at New York University and then went on to Seton Hall Law as the first
member of his family to pursue a legal education. At the Law School his personal and
professional lives both took shape. Read More >>
Alumnus Honors Her “Trailblazer” Father with Gift to Law School
Kimberly Hunter Turner ’90 sums up her father’s legacy by one word – trailblazer.
She’s certainly right about that: the Honorable Mac D. Hunter ’63 was only the second
African American to graduate from Seton Hall Law, and he blazed trails throughout
a remarkable legal career, now commemorated by a gift to the Annual Fund. Read More >>
Seton Hall Law's Weekend Program Draws Those Looking for Boost in Corporate World
From ROI-NJ: Michael Moreback doesn’t know where his law degree will lead him. As
a compliance officer with Wells Fargo, he enjoys the work he does. He just knows he
could do his job better — if he had a law degree. That’s why Moreback enrolled in
the new weekend program option offered by the Seton Hall University School of Law.
Read More
Ninth Annual Diversity Banquet
Hosted by Seton Hall Law Student Organizations, ALSA, APALSA, BLSA, Lambda Law Alliance
and LALSA, the Ninth Annual Diversity Banquet will host Keynote Speaker Julissa Reynoso,
Esq., Partner, Winston & Strawn LLP on the evening of March 21st. Read More >>
Seton Hall Law hosts Opioids: Care Coordination, Transitions, and Engagement
On February 22, Seton Hall Law hosted a one-day conference highlighting innovative
approaches improving transitions of care for individuals with opioid use disorder.
The impactful day kicked off with keynote speaker Gurbir S. Grewal, New Jersey Attorney
General. Read More >>
Celebrating Diversity in the Compliance Profession
On February 1, 2018, Seton Hall Law School's Center for Health & Pharmaceutical Law
& Policy hosted its annual Diversity in the Compliance Profession networking event.
This year’s program focused on Building Diverse Compliance Teams. Read More >>
For Seton Hall Law Alumni - It's All in the Family
Though they graduated from Seton Hall Law over 40 years ago, Kevin ’73 and Nan ’74
Prongay, have kept close ties with their alma mater, so maybe it’s not so surprising
that their son, Robert ’08 is also a proud alumnus. As Seton Hall Lawyers, the Prongay
family all feel strongly about being loyal supporters: “We wanted to give back to
the school that launched us on the profession we so enjoy,” says Nan. Read More >>
Second Annual Regional Health Law Works-in-Progress Retreat
On February 9, 2018, Seton Hall Law School’s Center for Health & Pharmaceutical Law
& Policy hosted its Second Annual Regional Health Law Works-in-Progress Retreat. The
purpose of the retreat is to give area area health law scholars an opportunity to
share their work and exchange ideas in a friendly, informal setting. Read More >>
Seton Hall Law's Mock Trial Team Awarded First Place
The Seton Hall Law Mock Trial team has been awarded first place in the Thurgood Marshall
Mock Trial competition during the Northeast Black Law Students Association Regional
Convention in Albany, New York. Read More >>
Seton Hall Law Featured in US News - "Use a Law Degree for Nonlegal Jobs"
Some people go to law school knowing they don't intend to practice law because they
plan on pursuing a law-related job in communications, politics or business.
“We know from experience that a fair percentage of our students already are coming
to law school intending to do something other than practice law," says Kathleen Boozang,
dean of the Seton Hall University School of Law. Read More >>
Are you worried about losing your child to a Smartphone?
Learn about the costs of excessive use of smartphone and screens and options available
to parents. Learn more and book a Parents Lecture now Read More >>
Seton Hall Law's Weekend Program featured in Faculty Lounge and TaxProf Blog
As the end of the first semester of the 2017-2018 academic year came to a close, Seton
Hall Law's inaugural Weekend class also experienced their first semester coming to
class on alternating weekends. Faculty Lounge and TaxProf Blog recently featured a
piece on Seton Hall Law's innovative Weekend JD Program and it's successes. Read More
Professor Lori Nessel Featured In the News for Her Expertise on Immigration
Seton Hall Law Professor and Director of the Center for Social Justice, Lori Nessel
was in the news in January 2018 for her expertise on immigration law. Nessel was interviewed
by Bloomberg, NJ.com, New Jersey 101.5, and NJTV News. Read More
Seton Hall Law Alumni Becomes Interim U.S. Attorney for N.J.
Attorney General Jeff Sessions announced the appointment of Seton Hall Law alumni,
Craig Carpenito '00 as Interim United States Attorney on January 3, 2018. Read More
Institute for Privacy Protection’s School Outreach Program
“Our program is unique in reaching students and parents, seeking to educate both about
the risks of privacy mismanagement and technology over-use and to foster trust as
parent-child relationships are increasingly affected by technology,” says Professor
Gaia Bernstein, Director for the Institute for Privacy Protection. Read More
Donor Helps Establish Bar Prep Assistance Fund
This fall, Walsh, Pizzi, O’Reilly, Falanga, LLP generously commited $100,000 to Seton
Hall Law to create a Bar Prep Assistance Fund that will provide financial assistance
to recent graduates during their bar examination preparation. Read More
From Opera Stages to Law Classrooms
From music conservatories to Seton Hall Law School, two first year students graced
the stage as opera singers prior to being aspiring lawyers. A Newark native, Caroline
Braga is back home after at opera career that began at the ripe age of nine. She went
to grade school at Wilson Avenue School, just down the street from where she now studies
Contracts and Civil Procedure. Read More
Seton Hall Law Features Experts in Privacy Protection and Social Media
With ever-growing social media trends, Seton Hall Law is at the forefront of privacy
protection education. On November 3, Seton Hall Law School's Institute for Privacy
Protection hosted a full day conference on "New and Nontraditional Actors in Privacy
and Social Media Regulation." On November 6, Professor Sarah Waldeck was a speaker
at Lehigh's Data X's symposium "TMI: The privacy risk of social media addiction."
Read More
Setonian feature: "Law Student Doesn't Let His Disability Define Him"
On paper, Joshua Cooper is like every other college student striving toward a bright
future, while also trying to balance a social life. Yet, many people fail to see the
similarities between themselves and Cooper as they focus their attention to one aspect
of his life: his wheelchair. At 18 months old, Cooper was diagnosed with spinal muscular
atrophy type II, a disease that affects the motor neurons of the muscles and the synapse.
Read More >>
SBA President published in Healthcare Financial Management Association Magazine
A recent issue of The Healthcare Financial Management Association's news magazine
features Seton Hall Law School's Student Bar Association President Jason Castle co-authoring
"Church-Affiliated Hospital Pension Plans Win Big In SCOTUS.
CSJ Student Wins Hague Convention International Custody Case
In September 2017, the Center for Social Justice celebrated a victory: the Family
Law Clinic successfully obtained the return of a nine-year-old girl to her mother
in Colombia after she had been wrongfully detained by her father in the U.S. for over
nine months. Read More
Seton Hall Law Hosts UN Accountability and International Law Experts Workshop
On Thursday, October 19th, a world class group of experts working in the United Nations
accountability field came to Seton Hall Law to share their research and expertise
through a number of moderated panel discussions. Professor Kristen Boon hosted the
workshop and delivered the welcome address. The keynote address was delivered by Philip
Alston, a UN Special Rapporteur. Read More
"Why Go to Law School?" from Professor Paula Franzese
Professor Paula Franzese is featured in the New Jersey Law Journal answering her top
five reasons of "why go to law school?" No matter the naysayers and outliers, the
legal profession is esteemed and noble. The good lawyer is an exemplar, able to show
the face of justice pursued. Read More >>
New and Nontraditional Actors in Privacy and Social Media Regulation Conference
Seton Hall Law's Institute for Privacy Protection will host a conference on "New and
Nontraditional Actors in Privacy and Social Media Regulation," on Friday, November
3rd. This conference will examine a growing trend of unexpected players filling in
the growing vacuum left by the federal government in privacy and social media regulation.
Register Now >>
Meet Sarah Hsu Wilbur, an Institute for Privacy Protection Student Fellow 2017-2018
Sarah currently is a junior associate in the Litigation practice group at Morgan,
Lewis & Bockius LLP. She works on a variety of cases in the areas of complex commercial
litigation, civil litigation, and regulatory enforcement and investigation, some of
which touch on privacy issues. She hopes to do more work in cybersecurity and data
privacy law as those opportunities present themselves. Read More >>
Meet Jason Sumbaly, an Institute for Privacy Protection Student Fellow 2017-2018
Jason Sumbaly JD/MA '19 was an inaugural Student Fellow with Seton Hall Law's Institute
for Privacy Protection in the 2017-2018 academic year. He thoroughly enjoyed teaching
young students about pressing issues such as online reputation, reputational harm,
the impact of online advertisements, and general online etiquette. Jason has long-recognized
the impact of social media, online advertisements, and the proliferation of internet
use among young students. Read More >>
Meet Yolanda, an Institute for Privacy Protection Student Fellow 2017-2018
Yolanda Bromfield graduated from Seton Hall Law School in 2018. Prior to attending
law school, Yolanda was a math teacher at Paul Robeson Charter School in Trenton,
New Jersey. Yolanda served as a corporate compliance fellow at Johnson & Johnson in
New Brunswick, New Jersey. While at J & J, Yolanda worked on various projects involving
clinical trials over social media and the privacy and FDA implications that arise
from engaging patients over the internet, as well as research on health care provider
contracts. Read More >>
Seton Hall Law’s weekend program embraces broader perspective on law degree
Dean Kathleen Boozang’s mantra for preparing students for the changing legal market
is “one student at a time,” assuring that all students have access to the school and
its facilities, creating opportunities and giving them the tools to adjust to life
after graduation. Read More
33rd Annual Red Mass
Cardinal Joseph W. Tobin, C.Ss.R., Archbishop of Newark, was the principal celebrant
and homilist at the Archdiocese’s 33rd Annual Red Mass. The Mass seeks guidance from the Holy Spirit for all those seeking
justice in the service of the law. Receiving the St. Thomas More Medal (and pictured
above with the Cardinal and Dean Kathleen M. Boozang) was Jeffrey S. Chiesa. Read
more.
National Jurist Ranks Seton Hall Law Among Best for Employment
In its Back to School issue, The National Jurist ranks Seton Hall Law #11 among law
schools across the nation overall with employment rates from 2011-2016. Thanks in
part to Seton Hall Law's Office of Career Services, graduates are becoming increasingly
successful in post-graduation employment. Read More >>
Dean Boozang Interviewed by NJTV
At a time when law school enrollments nationwide have remained flat or fallen, Seton
Hall Law has broken the mold. Its admissions up 33 percent. It’s national rankings
on the rise. What’s its secret? Seton Hall Law Dean Kathleen Boozang shares it with
Correspondent Lyndsay Christian. Read More >>
Orientation 2017: Dean Kathleen Boozang's Remarks
Seton Hall Law Dean Kathleen M. Boozang delivered opening remarks at the 2017 Orientation
for incoming and transfer students on August 16, 2017. “We have an obligation to produce
lawyers who can represent clients from all backgrounds with empathy. Empathy requires
us to have some sense of our clients’ lives, or the curiosity and skills to learn
about their lives.” Read Dean Boozang's remarks >>
Orientation 2017: Welcome, Students!
United States District Judge, for the District of New Jersey, The Honorable Susan
D. Wigenton will share welcoming remarks to the incoming Classes of 2020 and 2021
at Seton Hall Law's new student Orientation on Wednesday, August 16. The Law School's
Orientation schedule is filled with presentations, workshops, receptions, and great
opportunities for students to meet classmates and professors as they embark on their
first year of law school.
Professor and Alumnus Provide Help to Homeowner in Mortgage/Foreclosure Case
Making the news recently, Seton Hall Law Professor Linda Fisher and alumnus Joshua
Denbeaux '94, helped a homeowner who was denied a previously agreed upon modification
from her mortgage lender during foreclosure mediation. The borrower made all payments
in compliance with her part of the agreement, but the lender insisted on additional
concessions. Read More >>
Two sisters, two different Seton Hall Law degrees.
Two sisters, Brooke and Leigh Emery, arrived at Seton Hall Law on different paths,
both are pursuing educations that will inevitably advance their careers. Brooke Emery
“wanted to be a lawyer since I was five-years-old. I was a born arguer,” she jokes.
“I’d ask to watch Judge Judy instead of cartoons when I was younger.” Brooke started
out as a paralegal at a law firm and an intern with the Major Crimes Unit of the Sussex
County Prosecutors Office, both of which reinforced her passion for the law. Read More >>
What are Seton Hall Law students doing this summer?
Each summer, dozens of Seton Hall Law students fill legal positions in firms, private
practice, corporate/business entities, government roles, and public interest organizations.
These 2L and 3L students gain valuable experiences to further their careers as Seton
Hall Law's Office of Career Services acts as a partner for many of them providing
guidance and helping them to secure positions in fields of interest. Read More
Seton Hall Law Review Dedicates Current Issue to the Late Professor Marc Poirier
Volume 47, Issue 3 (2017) of the Seton Hall Law Review is dedicated to the legacy
of Seton Hall Law Professor Marc Poirier, who passed away in 2015. The four articles
- The Power of Empathy in the Classroom, Trademark Law in the Time of Kulturkampf:
The Poirean Perspective, A Research Agenda for the History of Property Law in Europe,
Inspired by and Dedicated to Marc Poirier, and Property without Personhood - all celebrate
Professor Poirier's work, wisdom, enthusiasm, commitment, and empathy. Read More >>
Senator Cory Booker and Professor Paula Franzese Advocate for Tenant Rights
U.S. Senator Cory Booker (D-NJ) met with housing advocates and New Jerseyans affected
by tenant blacklisting to discuss legislation he will introduce this week to reform
tenant screening practices. Landlords in New Jersey and across the nation are using
tenant screening reports prepared by third-party reporting agencies as a legal means
to discriminate against potential tenants for simply asserting their legal rights.
Sen. Booker’s legislation would amend the Fair Credit Reporting Act to enact stricter
regulations on tenant rating agencies and provide tenants additional protections.
Read More >>
US Healthcare Compliance Event Wrap Up
Seton Hall University School of Law held its annual U.S. Healthcare Compliance Certification
Program June 12-15 at the Law School, which has been taking place for the last 13
years.
With nearly 150 in attendance, guests were immersed in the statutes, regulations,
and other guidance that comprise the body of law known as “fraud and abuse law.” Read More >>
Rising 2L Has Employment Piece Published in National Law Review
Seton Hall Law student, Melanie Lupsa, never considered herself a strong writer but
her recently published piece in The National Law Review, “Mandated Individual Arbitration
in the Employment Context: The Debate over Federal Legislation's Impact on Employee
Rights, The Real Consequences, and the Need for Supreme Court Action” proves otherwise.
Although she recognizes how much her writing improved during her first year, it was
the “write-on” competition for the Law School’s three journals that was a game changer
for her. Read More >>
Seton Hall Law Professor Presented with Fulbright Grant
Seton Hall University School of Law Professor, Margaret Lewis, was recently awarded
a grant from the Fulbright U.S. Scholar Program to spend the 2017-2018 academic year
researching human rights and criminal justice reforms in Taiwan. She will be based
at Taiwan’s premiere law school, National Taiwan University. Lewis received one of
six annual Fulbright research grants awarded for the arts, education, humanities,
professional fields, and social sciences. Read More >>